Report: Destructive Malware Used to Target Olympic Infrastructure
Researchers said Monday the Olympics were hit by new and destructive data-wiping malware last week.
Deep in the Crypto Mines
The future of malware is here and it’s not coming for your data or your passwords or your bank account details. It’s coming for your computing power.
Jackpotting Attacks Hitting U.S. ATMs Per Secret Service
ATM manufacturers sent notices to banks late last week warning that "jackpotting" attacks have come to the U.S.
New Android Malware Families Loapi, GnatSpy Identified
Mobile security researchers discovered two new strains of Android malware, Loapi and GnatSpy, on Monday.
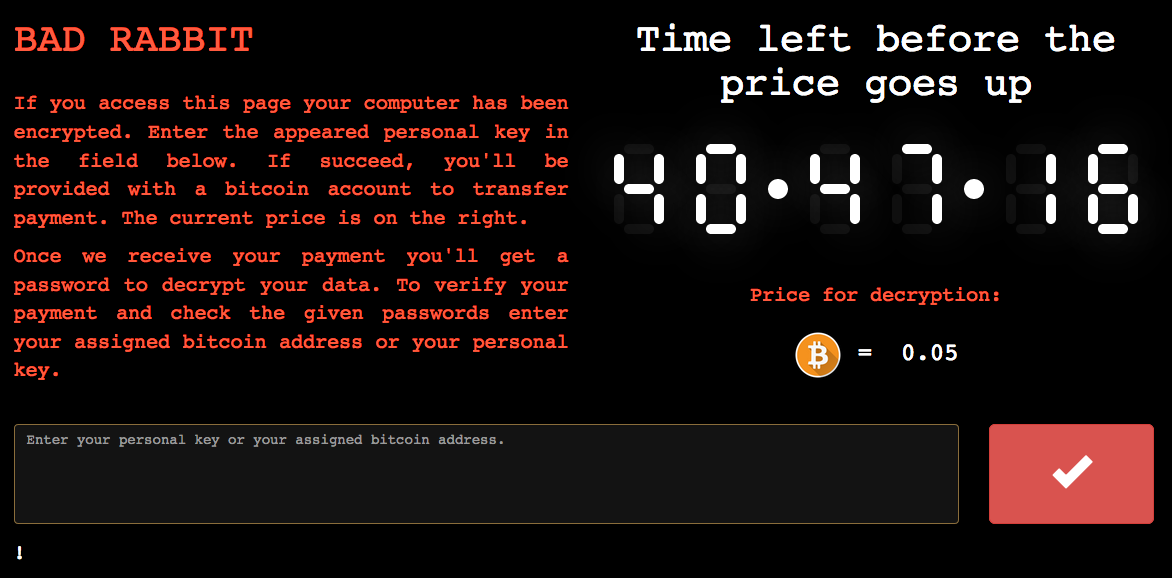
Bad Rabbit Ransomware Hits Russia, Ukraine
A previously unknown strain of ransomware, Bad Rabbit, hit roughly 200 targets across Russia, Ukraine, and Bulgaria, on Tuesday.
Taking Down an Android Botnet
A collaborative effort among more than half a dozen security and technology companies has disrupted a botnet that was attacking content providers and content delivery networks with compromised Android devices.
The Cost of a Malware Infection? For Maersk, $300 Million
The NotPetya fallout continues, with global transport and logistics conglomerate Maersk reporting up to $300 million in losses following a June cyber attack.
Merck Earnings Per Share Projections Drop following Malware Infection
With the release of its Q2 financial results, pharmaceutical giant Merck is the latest company to report material impact following malware infections.
BrickerBot, Mirai and the IoT Malware Knife Fight
The IoT landscape is becoming a battleground for all manner of malware, with some variants fighting for control of infected devices and authors racing to get their creations onto as many devices as possible.
Attack of the Killer Cameras
By now, you will be aware that the Internet of Things is a thing and that it is an ever-growing network made up of disastrously insecure appliances, vehicles, cameras, and other devices connected to the Internet. What you may not be aware of is that this shadow network is now being used as a weapon to attack web sites with DDoS floods with some of the highest volumes ever seen.
Don't Fall Behind
Get the latest security insights
delivered to your inbox each week.
Thank you for subscribing!