The Best Resources for InfoSec Skillbuilding
| Contact Us | |
| Free Demo | |
| Chat | |
Check out our guide to the top resources for information security skill building, from books to bootcamps.
Information Security has emerged as a growing industry for IT professionals to diversify their career path in the InfoSec direction. With the recent increase in the number of cyber-attacks on applications, networks as well as in cloud computing – resulting in massive data breaches and some of history's biggest ransomware attacks – it has become imperative for all enterprises to have a strong security team in place that follows standard security best practices coherent to the security policy. It's not an issue that's specific to one particular industry; data breaches occur across sectors such as healthcare, financial services, manufacturing, and more, all with the potential for dire consequences.
In response to the rise in data breaches, the European Union enacted GDPR, a regulation intended to protect the data privacy of EU citizens. The United States is following suit, with California forging the path with the California Data Privacy Protection Act and other states following with similar legislation. An increase in security risks, coupled with increasingly stringent regulatory requirements for companies, is driving an unprecedented need for trained, qualified, and highly skilled InfoSec professionals. As any InfoSec pro knows, education doesn't end with having a degree in hand. The ever-evolving threat landscape requires a commitment to ongoing skill building and continuing education. That's why we've compiled this list of resources including books, free training material, presentations, blogs and boot camps that will help you build your skills as an InfoSec professional.
- Books
- Free Training
- Presentations
- Blogs
- Bootcamps
- Virtual Labs
- Penetration Testing
- DevSecOps
- Resources for Kids to Learn About CyberSec
Books
1. Security in Computing (5th Edition)
This book gives complete coverage of computer security with an emphasis on networks, operating systems and software devices including data and multiple users. The new edition includes steps to prevent malicious code execution, best practices for authenticating users, detecting intrusion and much more. It also has end-of-chapter exercises to solidify concepts introduced in the book.
Key Takeaways:
- Vast coverage of security issues
- Guarding privacy threats
- Computer and cyber warfare – emerging risks and recent attacks
- Flaws and risks of electronic voting systems
2. Crafting the InfoSec Playbook: Security Monitoring and Incident Response Master Plan (1st Edition)
This book gives practical approaches to manage security. It teaches how to develop your own incident detection and threat intelligence instead of solely depending on security tools. It guides in making an InfoSec playbook by developing strategy, technique and architecture.
Key Takeaways:
- Incident response fundamentals
- Methods for security monitoring and response
- Selection of appropriate detection and monitoring tools
- Techniques to develop queries and sort through data
This book presents a comprehensive framework for managing all aspects of the organization's cybersecurity program. It gives guidance on methods to architect, design, implement and operate a cybersecurity program that meets the organization's policy, IT lifecycle and audit requirements.
Key Takeaways:
- Building a fail-safe cyberdefense system
- Architecting a cost-effective cybersecurity program
- Strategic and Tactical levels of explanation in all areas of cybersecurity
4. Security Controls Evaluation, Testing, and Assessment Handbook (1st Edition)
This handbook by Leighton Johnson gives a well-developed and most recent approach for the evaluation and testing of security tools to ensure that IT systems are functioning accurately. It gives an explanation of how to evaluate the effectiveness of security when systems are subjected to vulnerabilities or external and internal threats.
Key Takeaways:
- Guides to implement, monitor and evaluate security controls
- Methodologies for assessment, testing and evaluation of IT systems
- Proper reporting techniques
5. Digital Resilience: Is Your Company Ready for the Next Cyber Threat?
This book by Ray Rothrock starts out by talking about the 2013 Target attack which led to the compromised credit information of 40 million customers. These types of hacks are now preventable and Digital Resilience explores the many ways by which you can make your enterprise more secure by taking steps to contain attacks and monitor networks.
Key Takeaways:
- Assess the resilience of networks against attacks
- Response to data theft, downed servers, and malware
- Building resilience strategies
6. Hacking the Hacker: Learn from the Experts Who Take Down Hackers (1st Edition)
In this book, Roger A. Grimes gives an insight into the world of cybersecurity describing the details that run behind the scenes and introduces the people who are at the forefront of this technological arms race. Hacking the Hacker shares stories of twenty-six leading professionals ranging from white hat hackers to security researchers.
Key Takeaways:
- In-depth white hacking techniques
- Stories from the world's renowned computer security experts
- Network attacks, penetration testing, cryptography and social engineering
7. IT Security Risk Control Management: An Audit Preparation Plan (1st Edition)
Author Raymond Pompon assists in identifying the paradoxes of information security and helps by giving tools that integrate security controls with business processes. It also gives step-by-step guidance to craft a security program that is successful by using different techniques of risk analysis, change management, organizational thinking and out-of-the-box thinking.
Key Takeaways:
- Preparation needed to pass common audits such as SSAE-16, PCI-DSS and ISO 27001
- Calibrate scope and customization of security controls to meet enterprise policy
- Implementation of challenging processes
In this book. John Strand discusses some very creative counter-intuitive measures towards securing the data and application of the organization. It introduces cyber-security defense tactics that can annoy attackers and help in identifying who and where they are.
Key Takeaways:
- Legal ways to attack attackers
- Securing networks beyond traditional methods
- Offensive tactics to secure data and applications
This book explains the recent skills, weapons and tactics that can be used for ethical hacking. It teaches how hackers overtake network devices by gaining access and then inject malicious code to plunder applications and browsers.
Key Takeaways:
- Learn advanced reverse engineering tactics
- Hijacking servers and browsers the ethical way
- The business side of ethical hacking
10. Extrusion Detection: Security Monitoring for Internal Intrusions
This book by Richard Bejtlich is a comprehensive guide to mitigate, detect as well as prevent any security breaches. It teaches how to access threats from instrument networks, internal threats and how to detect anomalies in the architecture as to be able to respond promptly and efficiently when an attack occurs.
Key Takeaways:
- Theory, techniques and tools for protecting system networks
- Implementation of Layer 3 network access control
- Network forensics
- Advanced extrusion detection
11. Threat Modeling: Designing for Security 1st Edition
Adam Shostack is a threat modeling expert and shares his expertise from serving as a security development professional for threat modeling at Microsoft. The book explores different threat modeling approaches and teaches ways to address threats.
Key Takeaways:
- Essential how-tos for security and software developers
- Approach to different threat modes
- Actionable steps for software, operating systems and programming languages
Free Training
12. Cybrary
@cybraryIT

Cybrary offers free training that can help you advance to your next job or a new career. It provides hands-on experience and assesses your new skills through online assessment tools. Even with no experience you can learn new skills and work with industry-leading mentors.
Key Takeaways:
- Innovative experiential learning
- Practice test software
- Virtual lab environment
13. IASE

Information Assurance Support Environment (IASE) provides a number of security training courses for professionals as well as senior leaders. Their cybersecurity awareness course is developed by the Defense Information Systems Agency. The course can be taken online or could also be a group presentation led by a facilitator.
Key Takeaways:
- Knowledge check track
- Online assessment tools
14. InfoSec Institute
@InfosecEdu

InfoSec Institute offers quality security training both online and offline. It provides many courses that teach Ethical Hacking, Penetration Testing, Forensics, Information Security Training and Security Certifications.
Key Takeaways:
- Ethical Hacking Boot Camp
- Computer and Mobile Forensics Training
- CISSP Training Boot Camp
15. SANS Cyber Aces
@CyberAces

SANS Cyber Aces offers courses that are free and online, selected from The SANS Institute. The open courses are focused on the fundamentals of cybersecurity and are akin to the training offered to security professionals around the world.
Key Takeaways:
- Foundations of information security
- Security involved with operating systems, networking and system administration
- Open to participants with or without a quiz
Risk3sixty provides free information security training materials with a formal structure of exams and acknowledgment forms that need to be completed. The package is free for any company to use if they find it useful.
Key Takeaways:
- Educational blogs
- Free training videos
17. CyberDegrees

Cyber Degrees offer 'Massive Open Online Courses' (MOOCs). These are offered by universities, taught by faculty and freely available to anyone interested in cybersecurity. They have video lectures that are pre-recorded and need a time commitment of about 6 to 10 weeks. The assessment could be a hands-on project or peer to peer reviews.
Key Takeaways:
- Introduction to Cyber Security
- Securing Digital Democracy
- Designing and Executing Information Security Strategies
- Cybersecurity Specialization
18. InfoSec Skills Academy
@Infosec_skills
InfoSec Skills Academy offers streaming audio with synchronized slides which are delivered through a web browser for the learner to access remotely from their office or home. The academy offers financing options for a classroom as well as e-Learning courses with no hidden costs for mock exams, tests or quizzes.
Key Takeaways:
- Aptitude tests on various subjects
- Live classes open to the general public
- Ongoing subject competition and challenges
19. Open Web Application Security Project (OWASP)
@OWASP
The Open Web Application Security Project (OWASP) provides free training and is a source for unbiased information on best practices as well as advocates open standards in the field of Information Security.
Key Takeaways:
- OWASP Security Sheph e rd
- OWASP Web Testing Environment
- OWASP Defect Dojo
20. Harvard University's Belfer Center Cybersecurity Campaign Playbook
@BelferCenter

This free training in the form of a playbook emphasizes establishing a culture of security awareness which involves training the staff by setting an example. It also emphasizes using the cloud with proper security measures such as two-factor authentication and encrypting messages that have sensitive conversations and materials.
Key Takeaways:
- Managing Cyber Risk
- Steps to create a secure campaign
21. Surveillance Self-Defense: Tips, Tools & How-Tos for Safer Online Communications
@EFF

Surveillance Self-Defense provides an expert guide to protect you from online spying. It provides a tool guide and instructions on how to pick a secure application. It also has a guided tour that helps you browse through common security scenarios.
Key Takeaways:
- Assessing risks
- Creating stronger passwords
- Protecting social networks
- Enabling two-factor authentication
22. An Introduction to Cybersecurity Ethics Class via Markkula Center for Applied Ethics
@SantaClaraUniv

This ethics module for cybersecurity-related courses is free training offered to start a conversation about ethical theory and situations that cybersecurity professionals are likely to face in executing their role. The training allows students to go through reading materials that involve case studies as well as complete homework assignments.
Key Takeaways:
- Articles and case studies
- Engineering Ethics
- Ethics in Tech Practice
Presentations
23. Keynote: Hacking is Child's Play, Literally! - Reuben Paul, 11 Year Old Hacker, CyberShaolin Founder
@linuxfoundation
In this presentation 11-year-old Reuben Paul, aka Cyber Ninja, discusses and demonstrates how smart things are not necessarily secure. He shares his experience and stories of hacking toys and covers tools that can make connected systems insecure.
Key Takeaways:
- Demonstration of insecurities in smart technologies
- Real-world applications
- Understanding security threats
24. Big Game Theory Hunting: The Peculiarities of Human Behavior in the InfoSec Game
@BlackHatEvents
This presentation examines the traditional game theory and explains why behavioral game theory should take its stand in the defensive philosophy. It examines how human behavior can differ in games and how it can affect security if it is assumed that they will behave only rationally.
Key Takeaways:
- Examination of traditional game theory
- First principles of game theory
- Human behavior in games
25. Cryptography & Cyber Security with Cody Mercer at InfoSec World 2018
@TalkTechDaily
@Malwarebytes

In this presentation Cody Mercer from Malwarebytes, having over 15 years of experience in cyber security, shares valuable information that could help seasoned professionals as well as career-changers to learn and educate themselves about this highly important and ever-increasing field of cybersecurity.
Key Takeaways:
- Cyber Security education
- Cryptography experience
- Introduction to Malwarebytes
26. The Never Ending Hack Mental Health in InfoSec Community-Danny Akacki
@irongeek_adc
@DAkacki
Uploaded by Adrian Crenshaw, this presentation features Danny Akacki at CircleCityCon, who talks about mental health and its association with InfoSec. Akacki connects the different factors associated with the work environment to mental illness and addresses sensitive questions of family/friends support along with the effect of mental health on an individual's productivity and efficiency.
Key Takeaways:
- Signs of burnout
- Coping with loss
- Tips to deal with mental illness
27. Cybersecurity: Crash Course Computer Science #31
@TheCrashCourse

This presentation gives an in-depth view of how the minds of hackers combine malicious code with computers to generate multiple combinations that can easily hack into accounts. It offers a strategy on how to use access privilege, biometrics and strong passwords to secure data and applications on the network.
Key Takeaways:
- Strong password generation
- Techniques for cybersecurity
- Cyber Security against DOS, malware and brute force attacks.
28. Go to Hunt, Then Sleep
@BlackHatEvents

This presentation discusses how to decide what to hunt for when aiming at security. It also guides the viewer on the priorities that are important when designing your hunt plan. The explanation is done in a narrative story style that runs a memory map for you to remember the step by step instructions.
Key Takeaways:
- Prevention of targeted attacks
- First 5 hunts to run to catch the hackers
29. [WARNING]: "Angry, Annoying, Awkward Admissions" by Jayson Street
@SkyDogCon
![[WARNING]:](https://digitalguardian.com/sites/default/files/WarningSkyDogCon.jpg)
This keynote speech delivered by Jason Street at SkyDogCon is about issues that women deal with but are never spoken about in an open platform. Instead of presenting the confessions as merely women issues, he removes the gender barrier and talks openly about certain annoying barriers.
Key Takeaways:
- Issues in the field of InfoSec
30. Lessons on Human Vulnerability within InfoSec/Cyber
@cyberharibu
In this presentation, Harry McLaren, a cybersecurity consultant shares his experience with vulnerability, failure and the lessons that can be taken forward by professionals to help create a healthier and safer environment.
Key Takeaways:
- Understanding of human vulnerability
- Root cause analysis
- Useful resources
31. Infosec & failures
@angealbertini

This presentation by Ange Albertini stresses the fact of learning from other InfoSec failures. This, in turn, becomes knowledge that needs to be stored. Thus, it is a process that emphasizes content preservation to have a future trail of knowledge that can then act as a security model.
Key Takeaways:
- Content preservation
- Conference talks
- Resource books
32. Information Security (InfoSec) Skills - Talent and Market Insights
@handigitals
This presentation goes through various talent availability skills and their application in the market. It explains at length the application of Identity and Access Management in security along with Industry Acquisition and Merger timelines.
Key Takeaways:
- InfoSec skills
- Identity and Access Management
- Market Insights
33. Brennan Center for Justice: Securing Elections From Foreign Interference
@BrennanCenter
In a report format, Lorence Norden and Ian Vandewalker outline specific actions Congress and local election officials can take to insulate voting technology from continued foreign interference. The report, written during ongoing investigations into Russia's cyber attacks focuses on voter registration databases and voting machines.
Key Takeaways:
- Guidance to protect data
- Detailed security measures
Blogs
34. CryptoBuzz
@cryptobuzznews

CryptographyBuzz News Network (CBNN) is a leading information service and social media services company for information security as well as cryptocurrency and blockchain technology. The blog aims to provide verified content to inform and educate the global community.
Key Takeaways:
- Cryptography
- Hacks
- Ransomware
- Cryptojacking
- Malware
35. Cloud Academy
@cloudacademy

The Cloud Academy blog has numerous regularly posted content related to Cloud Security. Well-known industry experts talk about best practices, security culture, building security teams and many other ways to ensure your data is safe and secure in the Cloud.
Key Takeaways:
- Cloud Security related best practices
- Team building and corporate culture for information security

ISC(2) is well known for the Certified Information Systems Security Professional (CISSP) certification. Their blog has content related to numerous IT Security topics including Network and Operations Security.
Key Takeaways:
- Cloud Security
- Risk assessment
- Cybersecurity Workforce
37. DZone Security Spotlight
@DZone
Dzone Security Spotlight has regular content posted on various topics related to application security, web security and network security.
Key Takeaways:
- Cloud Infrastructure Security
- API Security
- Container Security
38. CyberSecurity Ventures
@CybersecuritySF

CyberSecurity Ventures provides predictions, insights and market data for cybersecurity companies, information security practitioners and government cyber defense leaders. Their blog provides content by leading researchers and is a trusted source for cybersecurity facts, figures and statistics.
Key Takeaways:
- Cybersecurity reports
- Analysis and Predictions
- Career opportunities in the field of Cybersecurity
39. InfoSec Institute
@InfosecEdu

InforSec Institute blog has regularly posted articles by a leading team of Information Security instructors and experts. Their wide range of security specific content is helpful to a diverse group of security personnel as well as students looking to build a career in the field of Information Security.
Key Takeaways:
- Best Practices in InfoSec
- InfoSec Institute News
- InfoSec Training
40. Digital Guardian
@DigitalGuardian
The blog by Digital Guardian is written by leading industry experts in the field of Information Security and provides the latest updates on the upcoming Acts and Laws regarding Information Security. The blog is also educational with diverse topics on security, threats and recent attack reports.
Key Takeaways:
- Data Loss Prevention Solutions
- Security Program
- Endpoint detection and response
41. Microsoft Security Response Center
@msftsecurity
The Microsoft Security Response Center features the latest thoughts, lessons learned and case studies by leading industry experts. The blogs range from security best practices and tips, to the latest technological advancements such as implementing artificial intelligence in cybersecurity.
Key Takeaways:
- Security innovation
- Intelligent security implementation
- Cybersecurity
Bootcamps
42. CISA Training Bootcamp
@InfosecEdu

The boot camp offered by InfoSec Institute is a five-day intensive seminar that primarily focuses on all the areas that are required to successfully attempt the CISA exam. It offers review courses that cover all the core sections along with sample exam questions that are encountered on the CISA exam.
Key Takeaways:
- Certified program
- Exam pass guarantee
43. Evolve Security Academy
@switchorg

This boot camp offers a holistic cybersecurity education and can be taken as a 17-week in-person course in Chicago or as a 15-week remote live instructor-led boot camp. The curriculum teaches Defense Architecture, Security Hardening, Vulnerability Management, Cryptography, Incident and Forensics. It gives students real work experience via assessment work for non-profit organizations.
Key Takeaways:
- Coding and Cyber Security
- Security and session storage
- Python and Command line programming
44. Cybersecurity Career Track
@Springboard
The Cybersecurity career boot camp will give you the necessary skills to make software and applications more secure, write a report on your findings after a vulnerability assessment and provide recommended improvements. It gives the candidate the necessary skills to get hired as an Application/Software security analyst role.
Key Takeaways:
- 1-to-1 mentorship from a cybersecurity expert
- Student advisor and community managers
- Job support from a personal career coach
45. Open Cloud Academy
@RackspaceOCA
The Open Cloud Academy offers this boot camp conducted by leading subject matter experts. It provides students with the confidence that comes along with the application of knowledge and skills that are provided by their unique hands-on learning approach.
Key Takeaways:
- Intro to Cyber Security
- Network Security Fundamentals
- CISSP
46. SecureSet Academy
@SecureSetHQ

SecureSet Academy provides a number of courses for a career in InfoSec. It combines hands-on lab experience with a theory for real-world experience. Their CORE program offered as a cybersecurity engineering course for 20 weeks can get you ready for a new career as a penetration tester, technical analyst or as an InfoSec consultant.
Key Takeaways:
- SecureSet Preparation Program
- Hunt Program
- PATH Part-time Program
47. From Apprentice to Master
@softwareguild

The Software Guild, created by a group of skilled developers, have a number of coding and security boot camps. Their boot camps implement a number of proven, verifiable methods that teach skills in a way that are easily understood and retained by the students.
Key Takeaways:
- Career preparation
- Alumni and Employer network
- Continued Learning
Virtual Labs
48. Virtual Hacking Labs
@vhackinglabs

Virtual Hacking Labs is an e-learning company for penetration testing and ethical hackers which offers access to over 35+ labs. It covers topics on vulnerability assessment, exploitation, privilege escalation and ethical hacking that teaches different types of attacks encountered in a real-world scenario.
Key Takeaways:
- 35+ vulnerable hosts
- Self-paced full penetration testing course
Hera Lab is the most sophisticated virtual lab on IT Security. It is used by many IT Security professionals to practice real-world scenarios built by IT Security research teams. One of its key features is that it provides a safe and isolated environment to practice IT Security.
Key Takeaways:
- Real world Hera Lab scenarios
- Networks deployed only for uses
- Fresh re-start option
50. NDG Labs
@netdevgroup
NDG labs offers two major products. NDG Online is targeted towards IT professionals offering courses with a "practice as you read" approach. NETLAB + hosts real IT equipment, virtual machines and curriculum content targeted at academic institutions.
Key Takeaways:
- Online content and coursebooks
- Lab exercises and assessments
51. Virtual Security Cloud Labs 3.0
@JBLearning
Virtual Security Labs provides a hands-on experiential learning environment within their labs. The labs reproduce the complex challenges of the real-world, integrated with key course concepts. The 'Virtual Sandbox' provides the student with instant, unscheduled access to 80 virtual labs and allows them to practice 'White hat' hacking on an actual IT infrastructure.
Key Takeaways:
- 80 Virtual Security Cloud Labs
- Progress Tracking, Collapsible Lab Frame, System Checker
- Saved States Feature
Penetration Testing
52. Offensive Security Certified Professional (OSCP)
@offsectraining
OSCP is the most respected certification for information security professionals and exhibits the mastery of the professional in their application of the practical comprehensive knowledge of the penetration testing process. An OSCP holder can exploit code, conduct remote attacks and deploy tunneling techniques to bypass firewalls.
Key Takeaways:
- 24-hour hands-on exam
- Creative problem solving and lateral thinking skills
- Practical understanding of the penetration testing process
53. Penetration Testing Practice Lab
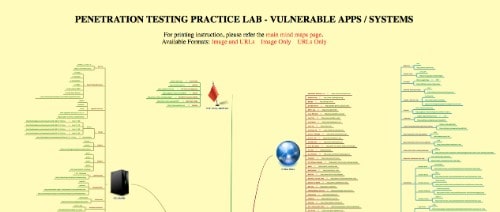
Information Security related mind maps give a detailed outline regarding security tests, securing home computers and cryptography. The Penetration Testing Practice Lab also has a detailed map of virus and worm classifications along with Hacking and Forensic challenges.
Key Takeaways:
- Vulnerable web applications
- Vulnerable operating system installations
- Vendors of Security Testing Software
54. Awesome Penetration Testing
@github
Nick Raienko, a full stack developer, has compiled numerous penetration testing resources for exploit development, social engineering, operating systems, networks as well as security courses that can be taken by IT professionals on GitHub.
Key Takeaways:
- Books, Tools and Resources for Penetration Testing
- Vulnerability Databases
DevSecOps
55. DevSecOps
@devsecops
DevSecOps focuses on developing security as a code so that innovation can be fostered to ensure data security. This type of thought process can lead to unlocking and unblocking new paths towards Information security.
Key Takeaways:
- Cloud Security
- DevSecOps Use Cases
- Security Science
56. DevSecOps 101
@ASPE_Training
DevSecOps emphasizes implementing security checks throughout the software development lifecycle instead of it being done just before deployment. This also helps in developing a strong feedback loop and a blameless culture between the development, security and operational teams.
Key Takeaways:
- Automation in Security
- Continuous failure injection
- Security as code
57. Secure Dev-Ops: A Practical Introduction
@SANSInstitute

This course gives an introduction to DevOps along with the tools, principles and best practices involved. It overlooks case studies of DevOps from industry leaders who have created the framework for DevOps. It explains the concept of Continuous Delivery (CD) and ways to map security controls into CD pipeline and automate security tests.
Key Takeaways:
- DevOps principles
- Continuous development pipeline
- Automated security testing
Resources for Kids to Learn About CyberSec
58. Savvy Cyber Kids
@SavvyCyberKids

Ben Halpert has taken up the mission to educate today's digital citizens in the workplace, at school, and at home. From preschool through high school, Savvy Cyber Kids provides cyber ethics awareness and educational sessions for students, parents, teachers and school administrators.
Key Takeaways:
- Program: Teaching with Technology
- Program: Digital Native and Digital Naïve
- Program: Technology, Privacy and You

Nova Labs provides a virtual environment wherein you are given tasks to strengthen cyber defenses and thwart attackers and also learn hacking techniques of cracking passwords, craft code and defeat malicious hackers.
Key Takeaways:
- Cyber Video Quizzes
- Video Library
- Interaction with the experts
60. Federal Trade Commission's You Are Here
@FTC
The Security Plaza module presented here teaches about the value of your personal information and the steps which can be taken to protect your data. It also educates about what to do when a laptop is stolen and ways to keep your computer secure.
Key Takeaways:
- Mail Security
- Network Security
61. Center for Cyber Safety and Education
@ISC2Cares
The Center for Cyber Safety and Education emphasizes the importance of teaching kindness and internet etiquette to children in today's interconnected world. It also helps children learn about safe posting practices and understand how to maintain privacy on the internet.
Key Takeaways:
- Privacy
- Dealing with Cyberbullying


