Digital Guardian Sponsors the Savvy Cyber Kids Super Fun Day
We’re proud to support youth technology education through our third year sponsoring the Savvy Cyber Kids' annual Super Run Atlanta. Read on for more about the initiative and how you can get involved!
Court Sides with Insurer: Credit Card Data isn’t Lost Property
A court in Alabama threw out a suit brought by a breached grocery store chain, saying that stolen credit card data doesn’t count as “damaged property.”
Cyber Needs More Perp Walks
The arrest of a 29-year-old man in Prague for suspected involvement in the 2012 hack of LinkedIn is a big victory for law enforcement. Even more important: viral video of the arrest.
The Good, the Bad, and the Cyber
As what is sure to be one of the more contentious presidential elections in recent memory approaches, The Cyber has become one of the dominant talking points for both candidates. Unfortunately, neither candidate seems to have a clear understanding of the basics of information security or a concrete plan for how to address the many security issues facing both consumers and businesses in the United States.
Introducing Data Insider, the new Digital Guardian Blog
Today we unveil an all new, redesigned Digital Guardian blog, DATAINSIDER.
Sign Up with the Usual Suspects: Consumer Breach Response is Broken and How to Fix It
The scourge of data breaches and identity theft is more than a decade old. But our tools for dealing with these common incidents are outdated and ineffective. Why?
Circle in Hell Awaits Habitat for Humanity Hackers
The Colorado branch of Habitat for Humanity says a long-running and “malicious” data breach started with ransomware in June, and is making it hard to even conduct business.
Yahoo Breach: User Data Considered Toxic
Computer science and security rely on precision for the descriptions of their constructs and concepts. But there are some things that defy description in these realms, and the Yahoo data breach is one of them.
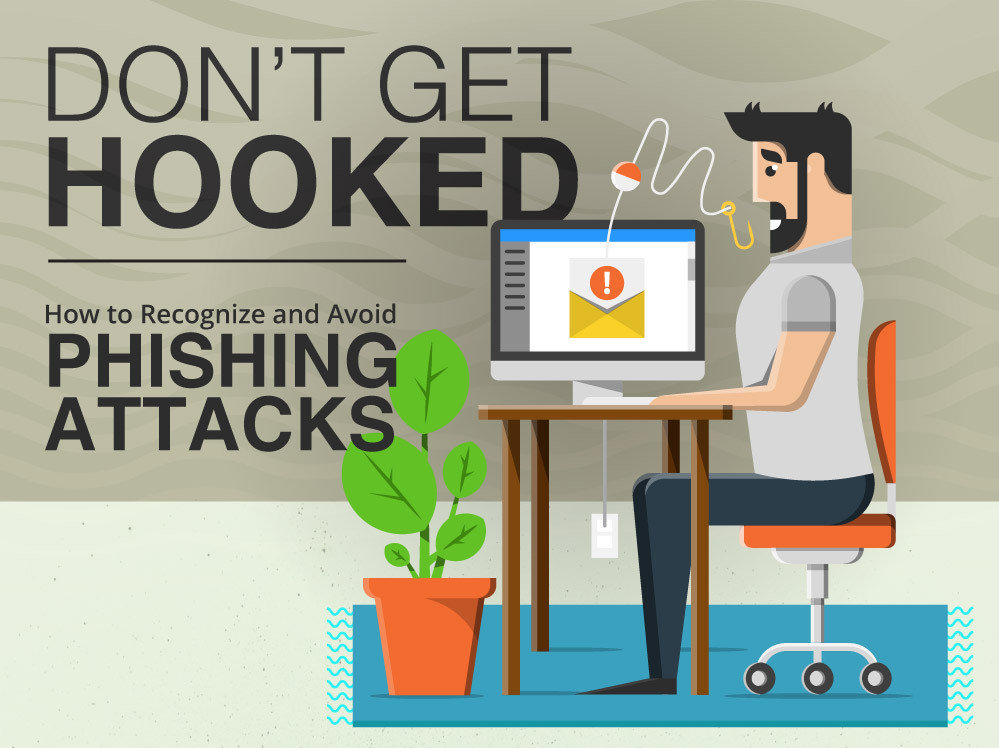
Don’t Get Hooked: How to Recognize and Avoid Phishing Attacks (Infographic)
We created an infographic to help spread awareness of one of the greatest and most common threats to computer users of all kinds: phishing attacks.
Less Than Zero (Trust): Learning the Lessons of OPM and WADA
A House Oversight Report Suggests the Zero Trust Model for Government Networks. What does that mean? And will it work?
Don't Fall Behind
Get the latest security insights
delivered to your inbox each week.
Thank you for subscribing!