Yearlong Office 365 Phishing Campaign Skilled at Evasion
| Contact Us | |
| Free Demo | |
| Chat | |
A new phishing campaign targeting Office 365 has used Morse code and other forms of obfuscation to side step detection for the last year.
Almost like a never-ending cat and mouse game, it’s become second nature for attackers to alter their techniques every so often in order to evade detection.
What's interesting is when researchers peel back the layers on an attack group and uncover just how often threat actors switch it up.
For example, attackers behind one recent phishing campaign that was targeting Microsoft Office 365 users earlier this summer changed their obfuscation and encryption mechanisms almost monthly, every 37 days approximately according to a recent Microsoft 365 Defender Threat Intelligence Team report.
To evade detection, the attackers broke the HTML attachment – an Excel spreadsheet file - into different segments an encoded them each differently almost a dozen times over the course of a year. What's more, at one point, the attackers used Morse code, the old and antiquated way to encode text characters, to hide JavaScript files essential to the attack.
The group refused to sit idle and as Microsoft's infographic, below, points out, used a different encoding mechanism each month, from July 2020 to July 2021. Naturally, the subject line lures changed every month, from "payment receipt" to "contract" to "payroll" and "purchase order," all topics designed to entice an employee to open the email.
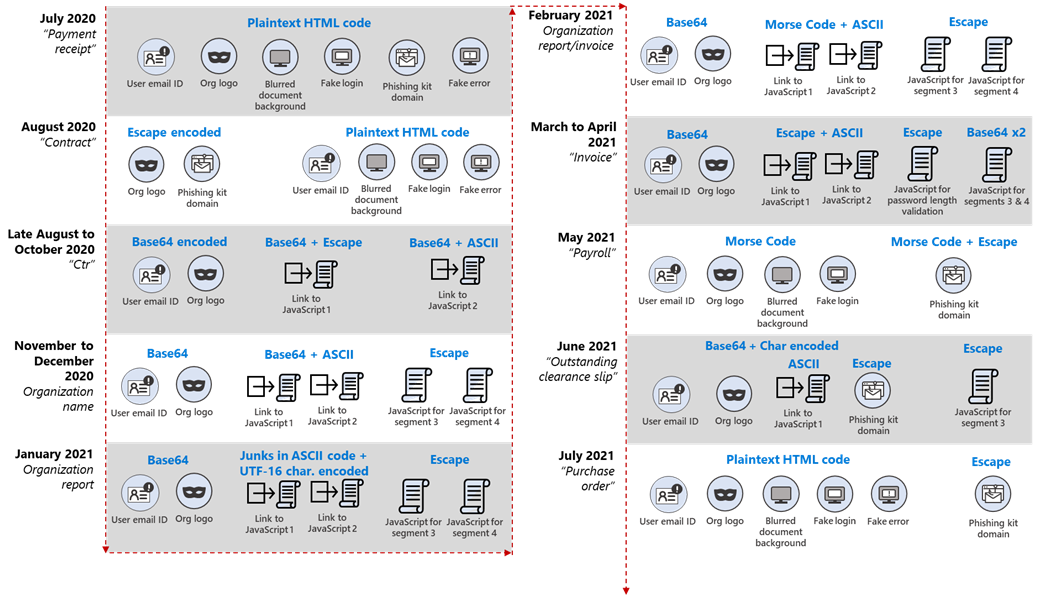
That in and of itself isn't surprising - attackers are constantly changing phishing email subject lines - what is interesting are the lengths the group went to skirt Microsoft's security controls. At first, back in July 2020 they used plaintext HTML code but moved away from that a month later by encoding their organization's logo and the phishing kit domain in Escape. Escaping is a form of encoding that sometimes involves adding a special character, like a backslash (\) before the character/string.
A month after that the group double dipped, first encoding links to JavaScript files in Base64, then in ASCII. The actual JavaScript files meanwhile were encoded in Escape.
Things started to get even more interesting, judging from Microsoft's report, in February, when attackers encoded links to the JavaScript files with ASCII, then encoded again in Morse code.
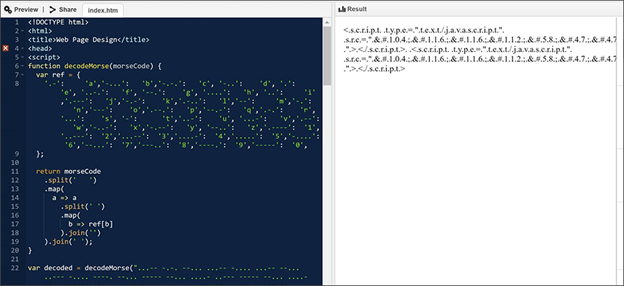
Two months later, in May, the group switched it up again, encoding the link to the phishing kit in Escape, then the entire HTML code in Morse code - a screenshot of the Morse code-embedded JavaScript below bares the hallmark dots and dashes of Morse code.
The group's most recent technique involves displaying a fake error message as soon as the user types their password; after that, the credentials are sent to the attacker's command and control server while the user is eventually routed to the legitimate Office 365 page, unaware they're been compromised.
Microsoft didn't disclose whether any of the attacks have been successful, or if the campaign is still ongoing.
It did however provide tips for users to help mitigate the group’s tactics, including:
- Using Office 365 mail flow rules or Group Policy for Outlook to strip .html or .htm or other file types that are not required for business.
- Turn on Safe Attachments policies to check attachments to inbound email.
- Avoid password reuse between accounts and use multi-factor authentication (MFA)
- Educate end users on consent phishing tactics as part of security or phishing awareness training.
Recommended Resources

All the essential information you need about DLP in one eBook.

Expert views on the challenges of today & tomorrow.

The details on our platform architecture, how it works, and your deployment options.
