What Should Businesses Know About NFTs and IP Protection?
29 Intellectual Property Experts & NFT Experts Reveal What Businesses Should Know about NFTs and IP Protection
Friday Five 12/2
World Cup scams and other international cybercrimes took the headlines this past week. Read about these threats and more in this week’s Friday Five!
What is a Proxy Server? Definition, How It Works & More
Proxy servers can add an extra layer of security for users and organizations alike. In this blog, we break down how proxy servers work and what their benefits are.
What is the Virginia Consumer Data Protection Act?
Learn why organizations will need to implement security practices to protect sensitive data under the Virginia Consumer Data Protection Act (VCDPA), set to go into effect in 2023.
What Are the Most Important Tips for Preventing Trade Secret Theft?
No matter what form they take, trade secrets can be incredibly valuable to a business. We asked 28 IP experts and business leaders what their most important tips are for keeping them safe.
Friday Five 11/18
Inadequate cybersecurity efforts, questionable data privacy practices, and ransomware made the top headlines this past week. Catch up on the latest stories in this week's Friday Five!
Easy Ways to Implement Vulnerability Management
Having a vulnerability management program in place - one that identifies and prioritizes fixing bugs in software - is a critical part of every organization's IT team.
Friday Five 11/11
LockBit may have taken a hit this past week, but that hasn’t stopped ransomware from making the headlines. Catch up on this and more in this week’s Friday Five!
What is DRM Protected Content? Definition, How It Works & More
What does it mean when digital content is DRM protected? We explain how DRM works and protects intellectual property in this blog.
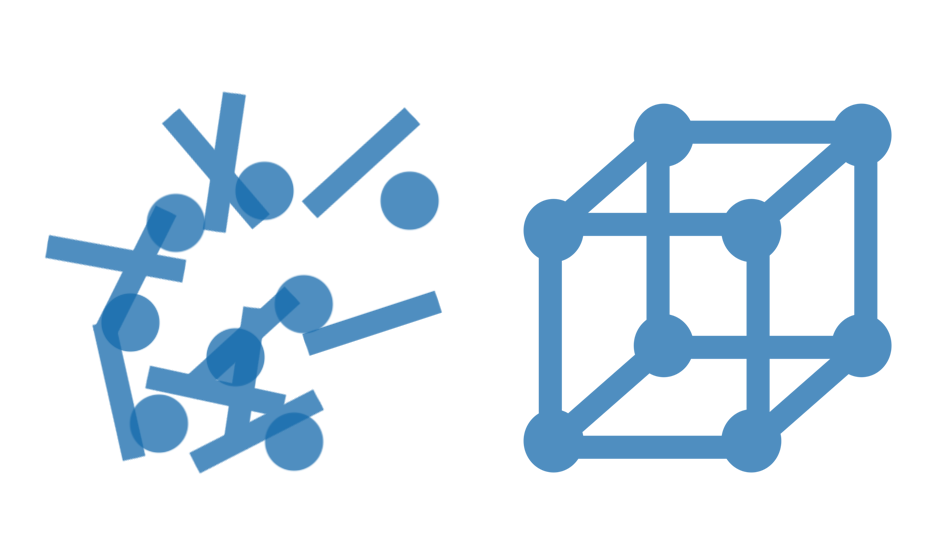
Structured vs. Unstructured Data: A Comprehensive Guide
Learn about the difference between structured data and unstructured data and how to best protect it in Data Protection 101, our series on the fundamentals of information security.
Don't Fall Behind
Get the latest security insights
delivered to your inbox each week.
Thank you for subscribing!