With the rising value and volume of digital assets, there’s greater risk of insiders leaking or stealing sensitive data. Once you grant insiders access to your network, perimeter security offers no protection. Bad actors enjoy the freedom that comes with trusted access and can compromise systems undetected. Guarding against insider threats requires a focus on understanding and securing the data itself and prompting users to do the right thing.
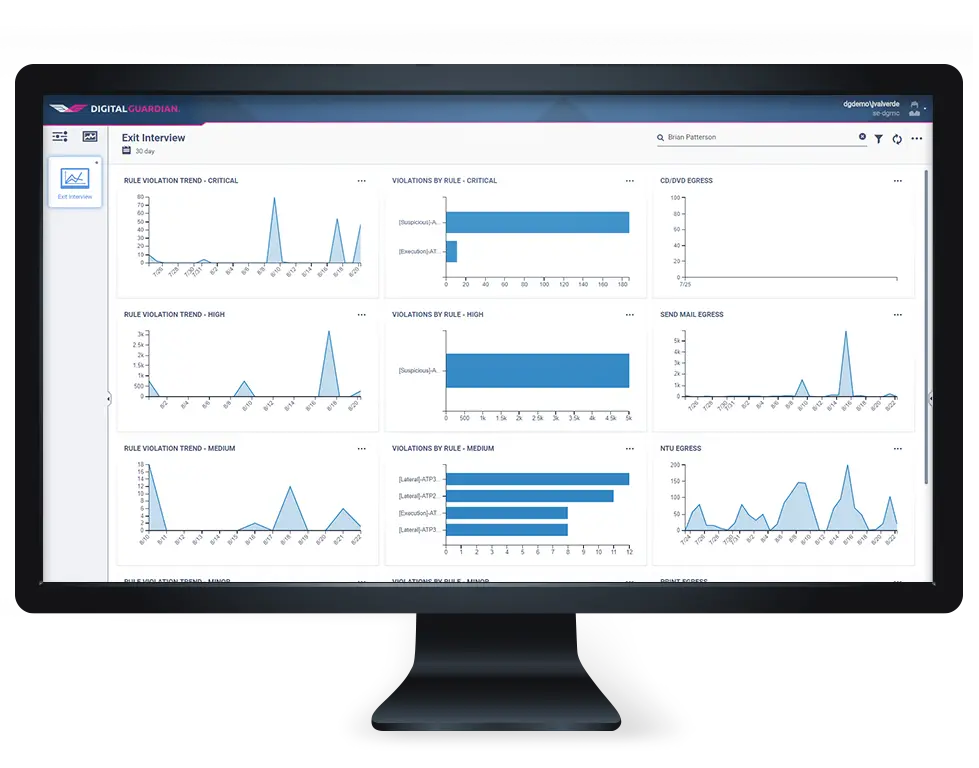
Digital Guardian’s threat aware data protection understands your data, how it moves, and when it is at risk from insiders. Our deep visibility locates and protects data throughout your enterprise and into the cloud. Real-time analytics understand what insider behaviors or actions represent risks, automated data classification highlights risky behavior targeting the most sensitive asset. Flexible, and automated controls allow benign actions but prompt at or block risky behavior, dramatically reducing insider incidents by changing user behavior with real-time education. All these combine to deliver the protection you need from insiders who may pose a risk to your security and compliance.
Solution Benefits
Stops Both Inadvertent and Malicious Insiders
Digital Guardian gives you the visibility into data movement and user activity to understand when insider actions represent a risk to data security or regulatory compliance and then applies the appropriate controls. Ranging from logging to automatic encryption or blocking, infosec teams have the power to stop the insider threat.
Digital Guardian gives you the visibility into data movement and user activity to understand when insider actions represent a risk to data security or regulatory compliance and then applies the appropriate controls. Ranging from logging to automatic encryption or blocking, infosec teams have the power to stop the insider threat.
Monitors and Controls Data Use of Privileges Users
Privileged users represent a great risk to the business given their broader access rights, Digital Guardian can enforce role-based access to sensitive information, and also apply specific controls based on the user action. Digital Guardian can confirm privileged users haven’t taken sensitive data prior to leaving the company.
Privileged users represent a great risk to the business given their broader access rights, Digital Guardian can enforce role-based access to sensitive information, and also apply specific controls based on the user action. Digital Guardian can confirm privileged users haven’t taken sensitive data prior to leaving the company.
Identifies Unusual Behavior
Digital Guardian baselines user activity, applications, and system configurations. If a behavior, action or configuration deviates from the expected, additional controls can automatically monitor or stop potentially risky actions.
Digital Guardian baselines user activity, applications, and system configurations. If a behavior, action or configuration deviates from the expected, additional controls can automatically monitor or stop potentially risky actions.
Dramatically Increases Policy Awareness and Secures Employee Behavior
Prompts on risky behavior train users in real time on the appropriate handling of sensitive data and discourage malicious insiders from completing actions. Digital Guardian customers report up to 85% decrease in prompts to users after just six months.
Prompts on risky behavior train users in real time on the appropriate handling of sensitive data and discourage malicious insiders from completing actions. Digital Guardian customers report up to 85% decrease in prompts to users after just six months.
The Power of Real-Time User Education
Learn how we provide data visibility, secure remote connections, and increased compliance policy awareness to a large managed healthcare provider.
Schedule a Demo
See how Digital Guardian can help protect your critical data wherever it lives.