2,500 of FBI's Counterintelligence Cases Linked to China
| Contact Us | |
| Free Demo | |
| Chat | |
The Federal Bureau of Investigation’s Director Christopher Wray discussed the Chinese Communist Party's vast influence on U.S. intellectual property, the financial sector, and democracy in a talk this week.
"If you are an American adult, it is more likely than not that China has stolen your personal data."
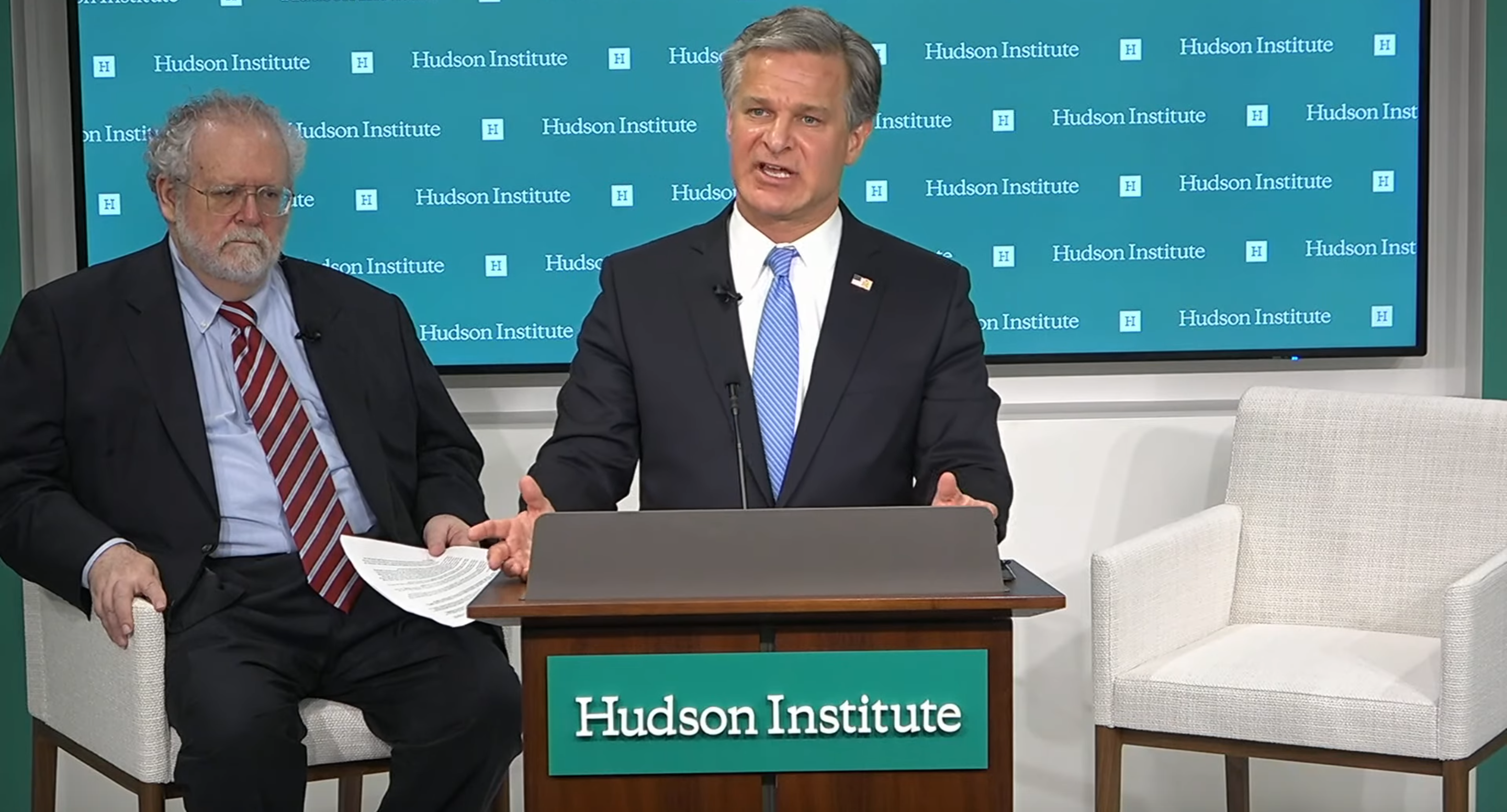
Those were just a few of the sobering words uttered by the Federal Bureau of Investigation’s Director, Christopher Wray, earlier this week at a discussion on China's attempts to influence elections, steal intellectual property, and meddle with the United States financial sector, held by Washington D.C.’s Hudson Institute. The institute, a think tank that specializes in analyzes US and international economic, security and political issues, streamed the discussion live on Tuesday.
While the fact that Chinese nation state attackers have your data may not be surprising, especially if you follow the news, perhaps more of a shock were some of the actual numbers Wray gave around China-related counterintelligence cases.
Wray told viewers of the video event that the FBI opens a new case related to China every 10 hours and that 50% of the roughly 5,000 active FBI counterintelligence cases - roughly 2,500 - relate to China.
Wray has given approximate numbers around counterintelligence threats before but not to this magnitude. He said last summer in a Senate Judiciary Committee hearing that the FBI has more than 1,000 investigations ongoing involving the theft of intellectual property in particular and that nearly all of them lead back to China.
China's behavior has stepped up in wake of the COVID-19 pandemic, with much of its activity centered around extracting intelligence from American healthcare institutions and pharmaceutical companies. Over the last decade, the agency has seen economic espionage cases related to China surge by 1,300 percent.
Wray's speech was yet another public indictment of China, specifically Chinese military-backed hackers with China's People's Liberation Army, by the government. The Justice Department charged four Chinese nationals for 2017's cyberattack against credit reporting bureau Equifax in February this year.
In addition to the Equifax hack, Wray cited a handful of incidents from over the years that were ultimately linked to China, including 2014's Office of Personnel Management hack and 2015's Anthem hack.
He also touched on China's "malign foreign influence" operations, efforts to pivot the country's policies, public discourse, and ultimately "undermine confidence in our democratic processes and values." While in the U.S., much of the talk around foreign influence has revolved around Russia's efforts to influence the U.S. election, Wray said China's efforts, which mostly rely on bribery, blackmail, and deals, are designed to shape policy and benefit China.
Identifying foreign influence operations has been an objective of Wray's since 2017, when he established a task force, the Foreign Influence Task Force, to identify threats to voting infrastructure, U.S. officials, and ultimately undermine confidence in democracy.
Wray lauded the FBI's successes, investigations that have resulted in prosecutions and elevated awareness around Chinese espionage threats, but stressed the U.S. needs a "whole-of-society response," one that holds the country's government responsible for violating U.S. laws.
“China, as led by the Chinese Communist Party, is going to continue to try to misappropriate our ideas, influence our policymakers, manipulate our public opinion, and steal our data. They will use an all-tools and all-sectors approach—and that demands our own all-tools and all-sectors approach in response,” Wray said.
Recommended Resources

All the essential information you need about DLP in one eBook.

Expert views on the challenges of today & tomorrow.

The details on our platform architecture, how it works, and your deployment options.
