4 Steps to Prevent Phishing Attacks (According to 33 Experts)
| Contact Us | |
| Free Demo | |
| Chat | |
What are the best ways to avoid and mitigate phishing attacks? We asked a panel of experts how not to fall victim to this popular cyberattack.
Phishing attacks are one of the most common security challenges that both individuals and companies face in keeping their information secure. Whether it's getting access to passwords, credit cards, or other sensitive information, hackers are using email, social media, phone calls, and any form of communication they can to steal valuable data. Businesses, of course, are a particularly worthwhile target.
How to Prevent Phishing Attacks
We asked this question to a panel of 33 infosec experts, and found these four commonalities among their responses:
- Conduct regular employee training: Train employees to recognize phishing attacks to avoid clicking on malicious links.
- Deploy a spam filter: Set up inbound spam filtering that can recognize and prevent emails from suspicious sources from reaching the inbox of employees.
- Keep passwords secure: Use a short phrase for a password (longer is better, and can be simpler) rather than just a few characters, and change it regularly. Deploy multi-factor authentication on critical business applications.
- Stay up-to-date with security patches and updates: You and your providers should install all the latest patches and updates to protect against vulnerabilities and security issues.
Common Types of Phishing Attacks Against Businesses
Company Impersonation
One of the most common forms of phishing is where attackers impersonate your brand. This is typically done with an email connected to a domain very similar to the target company (e.g., “first.name@amazon-support”). It’s also a difficult attack for companies to look out for due to the fact that you won’t know until someone falls for it or alerts you.
Spear phishing
Spear phishing is a type of scheme that involves using a fake company name (impersonation) but also key details about the target. Much like in sales, a rep finds the name, position and other personalization and includes that in a pitch email. Attackers find those same tokens and use it to compel more victims into their trap. It’s an especially dangerous ploy.
Email Account Takeover
All members of your executive and management team are vulnerable. If a phishing scammer acquires the email credentials of high-profile leadership, it’s likely they’ll target anyone they can using that very email address. Potential targets would be: colleagues, team members and even customers (if they’ve already obtained this information via hack).
Phishing Emails
Similar to the email account takeover scam, this phishing attack is done via email. The difference is the phishing scammer uses an email address that resembles a legitimate email address, person or company. The email will include a request to click a link, change a password, send a payment, respond with sensitive information, or open a file attachment.
Phone Phishing or Voice Phishing
Using Voice over Internet Protocol (VoIP) technology, scammers, again, impersonate companies. This technique also employs the other types of phishing including using personal details about targets and impersonating individuals of the company (e.g., the CEO) in order to get a higher take on the overall scam.
Phishing Attack Prevention Tips from the Experts
To help businesses better understand how they can work to avoid falling victim to phishing attacks, we asked a number of security experts to share their view of the most common ways that companies are subjected to phishing attacks and how businesses can prevent them. Below you'll find responses to the question we posed:
"How do companies fall victim to phishing attacks and how can they prevent them?"
Meet Our Panel of Data Security Experts:
Tiffany Tucker
Tiffany Tucker is a Systems Engineer at Chelsea Technologies. She's worked in the IT field for about 10 years. She has a Bachelor's degree in Computer Science and a Master's degree in IT Administration & Security.
The one mistake companies make that leaves them vulnerable to phishing attacks is...
Not having the right tools in place and failing to train employees on their role in information security.
Employees possess credentials and overall knowledge that is critical to the success of a breach of the company's security. One of the ways in which an intruder obtains this protected information is via phishing. The purpose of phishing is to collect sensitive information with the intention of using that information to gain access to otherwise protected data, networks, etc. A phisher's success is contingent upon establishing trust with its victims. We live in a digital age, and gathering information has become much easier as we are well beyond the dumpster diving days.
There are various phishing techniques used by attackers:
- Embedding a link in an email that redirects your employee to an unsecure website that requests sensitive information
- Installing a Trojan via a malicious email attachment or ad which will allow the intruder to exploit loopholes and obtain sensitive information
- Spoofing the sender address in an email to appear as a reputable source and request sensitive information
- Attempting to obtain company information over the phone by impersonating a known company vendor or IT department
Here are a few steps a company can take to protect itself against phishing:
- Educate your employees and conduct training sessions with mock phishing scenarios.
- Deploy a SPAM filter that detects viruses, blank senders, etc.
- Keep all systems current with the latest security patches and updates.
- Install an antivirus solution, schedule signature updates, and monitor the antivirus status on all equipment.
- Develop a security policy that includes but isn't limited to password expiration and complexity.
- Deploy a web filter to block malicious websites.
- Encrypt all sensitive company information.
- Convert HTML email into text only email messages or disable HTML email messages.
- Require encryption for employees that are telecommuting.
There are multiple steps a company can take to protect against phishing. They must keep a pulse on the current phishing strategies and confirm their security policies and solutions can eliminate threats as they evolve. It is equally as important to make sure that their employees understand the types of attacks they may face, the risks, and how to address them. Informed employees and properly secured systems are key when protecting your company from phishing attacks.
Arthur Zilberman
Arthur Zilberman emigrated from Minsk, Belarus and grew up in Sheepshead Bay, Brooklyn. He obtained his B.S. in Computer Science from the New York Institute of Technology, propelling him into his career as a corporate IT manager and later a computer services provider. Arthur Zilberman is CEO of LaptopMD, a staple of the New York technology community since 1999.
The one mistake companies make that leads them to fall victim to phishing attacks is...
Careless internet browsing.
Companies fall prey to phishing attacks because of careless and naive internet browsing. Instituting a policy that prevents certain sites from being accessed greatly reduces a business' chance of having their security compromised.
It's also important to educate your employees about the tactics of phishers. Employees should be trained on security awareness as part of their orientation. Inform them to be wary of e-mails with attachments from people they don't know. Let them know that no credible website would ask for their password over e-mail. Additionally, people need to be careful which browsers they utilize. Read all URLs from right to left. The last address is the true domain. Secure URLs that don't employ https are fraudulent, as are sites that begin with IP addresses.

Mike Meikle
Mike Meikle is Partner at SecureHIM, a security consulting and education company that provides cyber security training for clients on topics such as data privacy and how to minimize the risk of data breaches. He has worked within the information technology and security fields for over fifteen years and speak nationally on risk management, governance and security topics. He has presented for Intel, McAfee, Financial Times, HIMSS and for other Fortune 500 companies. He is also published writer with articles that have appeared in American Medical News, CNBC, CIO Magazine, Los Angeles Times and Chicago Tribune. He holds a Certified Information Systems Security Professional (CISSP), a Project Management Professional (PMP) and Six Sigma Green Belt.
There are several human and technological factors that companies should consider to avoid falling victim to phishing attacks:
On the subject of security breaches and social engineering, some of the most high profile breaches (Target, Sony) were instigated with phishing campaigns. In the case of Target, a 3rd party was compromised via email which allowed the malicious actors to eventually access the Target network.
Phishing/whaling is one of the key components of social engineering. The emails are crafted to resemble correspondence from a trustworthy source (government, legal, HR, bank, etc.) and often dupe individuals to click on a malicious embedded link. More sophisticated phishing emails execute hidden code if the mail is simply opened on the target’s computer.
Employees need to make sure that they understand the risks when opening email attachments or clicking on links from unfamiliar sources, for these can lead to malware or virus infection. This is best covered in an effective security education program.
A big component of protecting against phishing is employee training that actually works. Most security training delivered in the enterprise today is either a yearly event or held at employee orientation. If the training is given online the employees rapidly click through the content, ignoring most of the information. This is usually done at lunch while surfing other content. If actually given in person, the training is usually a deck of PowerPoint slides in small font narrated by an uninterested speaker for an hour. The enterprise really needs an effective Training, Education and Awareness (TEA) program for security.
There are several different technological approaches to combating phishing attacks. Certain products send test phishing emails to corporate staff which then provide metrics to security leadership about the efficacy of their anti-phishing training programs. The quality of these can vary but Wombat is a popular product in this space.
Another technological approach is to use a heuristics product to determine if an email is fraudulent. The success rate of these solutions is mixed. They filter out many of the obvious scams, but leave the more cleverly designed emails intact. IronPort is a leader in this niche. Outside of attempting to control social engineering exploits, businesses can also manage risk by investing in cyber security liability insurance. The ROI for this type of policy would have to be weighed against the business model, the data stored and the potential damages they could incur in the event of a data breach.

Steve Spearman
Steve Spearman is the Founder and Chief Security Consultant for Health Security Solutions. He has been employed in the healthcare industry since 1991, when he began working with Patient Care Technologies, an electronic medical record solutions provider. As Chief Security Consultant, Steve stays busy providing HIPAA risk analysis for clients and business partners. In addition to his duties at Health Security Solutions, Steve also serves as a member of the Health Care Advisory Council of Ingram Micro, as a speaker for Comp-TIA, and a consultant for state Regional Extension Centers such as CITIA and GA-HITREC, among others. Steve resides in Clemson, SC with his wife Jean, their three kids, and Gypsy, the InfoSec Media Wonder Dog.
The one thing companies need to keep in mind for phishing attack protection is...
Defending against these attacks requires a coordinated and layered approach to security:
- Train employees to recognize phishing attacks to avoid clicking on malicious links. For example, if the domain of the link to which you are being directed doesn't match the purported company domain, then the link is a fake.
- Many spam filters can be enabled to recognize and prevent emails from suspicious sources from ever reaching the inbox of employees.
- Two factor authentication should be deployed to prevent hackers who have compromised a user's credentials from ever gaining access.
- Browser add-ons and extensions can be enabled on browsers that prevent users from clicking on malicious links.
Phishing is a method used to compromise the computers of and steal sensitive information from individuals by pretending to be an email from or the website of a trusted organization. For example, a person receives an email that appears to be from the recipient's bank requesting that recipient verify certain information on a web form that mimics the bank's website. When captured by the hackers, the data allows them access to the recipient's banking information. Alternatively, the web-link may contain malicious code to compromise the target's computer. One of the things that makes phishing attacks tricky is that they can be distributed by compromising the email address books of compromised computers. So the email may appear to have been sent by a known and trusted source.
A subset and highly effective form of phishing attack is a spear-phishing attack in which a hacker will research an intended target and include details in an email that makes the email seem more credible. The details may, for example, reference a corporate social event from the previous month that was published on a public website. It can be exceedingly difficult to protect against these kinds of attacks as demonstrated by the notable and extremely costly breaches of sensitive information by Target, Home Depot, and Baylor Regional Medical Center.

Dave Jevans
Dave Jevans is Marble Security's CEO, chairman and CTO. He also serves as chairman of the Anti-Phishing Working Group, a consortium of 1,500+ financial services companies, ISPs, law enforcement agencies and technology vendors dedicated to fighting crimeware, email fraud and online identity theft. The APWG hosts eCrime, an annual symposium on electronic crime research that takes place in Barcelona, Spain.
Securing BYOD and educating end users is critical for phishing attack protection.
A new threat vector that has been introduced by the BYOD trend is that apps on employees' mobile devices can access their address books and export them to sites on the Internet, exposing the contacts to attackers who use them for targeted spear phishing. One important step for businesses to take is preventing prospective attackers from accessing the corporate directory, which includes names, email addresses and other personal employee information. Installing mobile security software on user devices that scans apps and prevents users from accessing the corporate networks if they have privacy leaking apps is recommended.
Another step is to protect mobile users from visiting phishing sites, even when they are on a Wi-Fi network that the company does not control. These protections must be done at the network level because email filtering is not sufficient. Phishing and spear phishing attacks can be delivered through corporate email, through a user's personal email that may be connected to their mobile device or through SMS messages to the user. Mobile users should be connected over Virtual Private Networks (VPNs) to services that provide secure Domain Name System (DNS) and blacklisting to prevent access to phishing sites.
Also, it turns out that the users themselves are often the best channel through which to detect, report and defend against phishing attacks. An important practice enterprises should implement is to put in systems where users can quickly and easily report a phishing attack, have it routed to IT, have it filtered and have it put in a system so that IT can quickly and easily add it to blacklists that will protect both internal employees and those that are remote or on mobile devices.

Greg Scott
Greg Scott works for Infrasupport Corporation. He published a fiction book, Bullseye Breach, about a large retailer that loses 40 million credit card numbers to some Russian criminals.
One key fact to remember when it comes to protecting against phishing attacks is...
All it takes is one employee to take the bait.
In a company with, say, 1000 employees, that's 1000 possible attack vectors. The IT department can set up inbound spam filtering and outbound web filtering. They can run security drills, education campaigns, and spend enormous amounts of money to monitor traffic in detail. These are all helpful, but all it takes is one person, one time, to become careless and fall prey to an online con job - which should be the real name for a phishing attack.
So how to prevent them is the wrong question to ask. A better question is, how to limit the damage any successful phishing attack can cause. Here, a few low cost tactics will offer a high reward. In retail - isolate those POS terminals from the rest of the network. Sharing should be baked into security practices everywhere. This is counter-intuitive, but the best way to defend against attack is to share how all the defenses work. In detail.
In cryptography, the algorithms are public. Everyone knows them. That's why we have strong cryptography today - the surviving algorithms have all been peer and public reviewed, attacked, and strengthened. CIOs should operate similarly. Openly discuss security measures, expose them to public and peer review, conduct public post mortem incident reviews, publish the results, and adjust the methods where necessary.
Bad guys are already reviewing, discussing, and probing security in the shadows. Bad guys have a whole supply chain dedicated to improving their ability to plunder, complete with discussion forums and specialists in all sorts of dark endeavors. The bad guys have unlimited time and creativity and the good guys are out gunned and out manned. Against such an adversary, what CIO in their right mind would want to stand alone? Smart good guys should join forces out in the open for the common good.

Jared Schemanski
Security Analytics Team leader, Jared Schemanski works at Nuspire Networks.
The technique of phishing is probably one of the easiest and hardest things to stop because...
This type of attack is predicated on sending out a bunch of random emails and thereby forcing people to click on a link that opens up a whole franchise to vulnerabilities. Then there is spear phishing which is highly personalized emails that go to a person higher up in an organization who has greater access than typical phishing email targets.
Tips on how to avoid phishing consist of non-technical safeguards since the user must click on an untrusted source that enters through an outward-facing environment. The best and sometimes only way to address this is to show employees how to read emails, thereby reducing the knee-jerk reaction.
Here are a few other tips to share with email users:
If the email comes directly from an acquaintance or source that you would typically trust, forward the message to that same person directly to ensure that they indeed were the correct sender. This means, do not simply just hit reply to the email with whatever information was requested in the email.
Similarly, when you receive an email from a trusted source and it seems phishy (pun intended), give that person a call directly and confirm that the email was from them.
You’ll be able to check to see what is or what is not legitimate by dragging your cursor over the email sender as well as any links in the email. If the links are malicious, they will likely not match up with the email or link description.

Luis Chapetti
Luis A. Chapetti is a Software Engineer and Data Scientist at Barracuda. Luis is part of the Barracuda Central Intelligence Team where he wears various hats handling IP reputation systems, Spydef databases and other top security stuff on the Barracuda Real-time protection system.
The one mistake companies make that leads them to fall victim to phishing attacks is...
Phishing today has become about as mainstream as a typical spam was back in 2004, basically meaning no one is immune to a possible phishing attack. One new way we've seen are campaigns that use embedded Excel spreadsheets. The spammers break the words into individual cells to bypass anti-spam tools. When viewed in an email it looks like a typical HTML attachment but it's much more difficult to analyze.
Here are a few tips to avoid being hit by such attacks for everybody:
- Always treat your email password like the keys to the kingdom, because that's what it is for spammers.
- Use a short phrase for a password (longer is better, and can be simpler) rather than just a few characters, and change it regularly.
- Never share your email passwords unless you are logging in to your email provider's website.
- Never click on links in an email - always type the address directly into the address bar.
- Keep your desktop AV, anti-spam, etc. up to date.

Felix Odigie
Felix Odigie is CEO of Inspired eLearning.
The most important thing to remember to avoid falling victim to phishing attacks is...
Education is the key.
No matter what people read or see in the news, when that phishing email lands in the inbox, they honestly don't know what separates that email from a real communication. In order to improve phishing awareness, companies should regularly test employees with fake phishing emails. This method enables employees to recognize what is real and what is a phishing attack.
No matter how secure a company's IT security platform is, the company is only as secure as its user base. Unfortunately, compromised credentials represent the vast majority of hacks (over 90%) and phishing and spear phishing attacks are responsible for the majority of those breaches. So, with all the investment capital devoted to securing IT infrastructure, how can companies prevent employees from opening phishing emails? The best answer is continuous, hands-on employee education.

Abhish Saha
Abhish Saha is the Chief Product Officer at Linkly. Throughout his twenty year career, he has been involved in consultations with some of the largest Australian and global businesses in Online Retail, Government Agencies and Billers. He has in-depth experience in leading developments across eCommerce, Technology, Business Banking, Risk Management, Security and Payment Gateways.
Securing against phishing attacks requires businesses to keep up with the ever evolving threat of phishing.
Phishing has become far more sophisticated than a suspicious email tempting a random individual to click on a link or provide their personal details. Usually phishing focuses on targeting an individual.
Here are three key phishing techniques that compromise companies to obtain several individuals' details:
- DNS-based phishing compromises your host files or domain names and directs your customers to a false webpage to enter their personal or payment details.
- Content-injection phishing is associated with criminal content, such as code or images, being added to your or your partners' websites to capture personal information from your staff and customers such as login details. This type of phishing often targets individuals that use the same password across different websites.
- Man-in-the-middle phishing involves criminals placing themselves between your company's website and your customer. This allows them to capture all the information your customer enters, such as personal information and credit card details.
Four ways that companies can defend against phishing attacks include:
- Use an SSL Certificate to secure all traffic to and from your website. This protects the information being sent between your web server and your customers' browser from eavesdropping.
- Keep up to date to ensure you are protected at all times. You and your providers should install all the latest patches and updates to protect against vulnerabilities and security issues. This includes website hosting, shopping cart software, blogs and content management software.
- Provide regular security training to your staff so that they are aware of and can identify phishing scams, malware and social engineering threats.
- Use a Securely Hosted Payment Page. This is the best practice for reducing risk to your customers' card data. Use a payment gateway provider that has up-to-date PCI DSS and ISO 27001 certifications from independent auditors. This ensures that your customers' payment details are protected at all times.

Jayson Street
Jayson is a well known conference speaker, and author of the book “Dissecting the hack: The F0rb1dd3n Network.” He has spoken at DEFCON, DerbyCon, UCON & at several other conferences and colleges on a variety of Information Security subjects. He is an Infosec Ranger at Pwnie Express.
Companies are falling victim to phishing attacks from both educational and technical standpoints.
From the educational standpoint, enterprises are not preparing end users correctly, and need to educate employees on evolving attacker methods. Companies have traditionally done a good job educating employees on standard phishing emails that are often poorly worded, and not well executed - making them easy to spot. However, advances in spear phishing have made attacks targeted, highly relevant and personalized with the help of social media.
It's no longer enough to watch out for crudely worded emails - recipients must also consider context, content and sender, particularly if monetary transactions are involved. Concerted coaching to teach employees to be vigilant by not clicking suspicious links or downloading attachments is critical. To verify authenticity, employees should cross check by sending a separate followup email, texting the alleged sender or even calling to validate that the email is from the correct source.
From the technical standpoint, too many companies allow full egress out of the network, rendering loopholes to external security measures. A well structured security system should have strong policies dictating the uses for inbound and outbound gateways through the firewall. But enterprises can’t only monitor what's coming into the network, they need to better monitor and curtail traffic going out of the network with DLP and outbound email scanning tools.

Patrick Peterson
Patrick is Agari's visionary leader and a pioneer in the email business. He joined IronPort Systems in 2000 and defined IronPort's email security appliances. He invented IronPort's SenderBase, the industry's first reputation service. In 2008, after Cisco's acquisition of IronPort, Patrick became one of 13 Cisco Fellows, where he led breakthrough cybercrime research focused on follow-the-money investigations into spam, scare ware spyware, web exploits, and data theft.
One thing to remember to avoid being susceptible to phishing attacks is...
Phishing attacks constantly happen. If someone came up to you on the street and said they had a package for you, you would say no thank you and walk away. When people get emails that say, FedEx has a package for you, they think that because it's on a computer screen they should click the link or open the attachment. A good rule of thumb is to take the same precautions you take online as you would in the real world.
Similarly, when it comes to passwords, if you happen to forget yours you can have it reset by answering personal questions. Those questions were once secure, but now many of the answers can be found on your social media accounts: birthdate, hometown, high school, etc. Think about what you share on social media in terms of being useful to cyber criminals.
Any company can take recent security breaches as more cautionary tales about the need for succinct security practices to protect company and consumer data. A very important aspect in email security is making sure your email provider uses technology like DMARC. It's the only email authentication protocol that ensures spoofed emails do not reach consumers and helps maintain company reputation. Top tier providers like Google, Yahoo, Microsoft and AOL all use it to stop phishing.

Daniel DiGriz
Daniel DiGriz is a digital strategist and CEO of MadPipe, which helps companies solve human problems with processes and technology. He has a master's degree in Instructional Technology, and several decades of background in technical fields with Fortune 500 companies.
The one mistake companies make that leaves them susceptible to phishing attacks is...
Companies with an authoritarian hierarchy run more risk for phishing attacks, because employees tend to be cooperative with schemes that sound authoritative. This is also true in some organizational cultures where it's frowned upon to ask for help, there's some degree of mutual distrust, or a less collaborative work model. When university staff get an e-mail that says someone may be trying to take over your e-mail account; please update your information, there's a perfect brew of an authoritative instruction, warning, and panic over who is looking at your work. In short, there's a high motivation to click.
Asking for IT help might create a backlash, so someone clicks, and it only takes one vulnerable recipient to give a phishing expedition what it needs to succeed. The odds go up when there are pockets of personnel who lack a basic level of technical literacy. Announcements about phishing may only cover one or two examples of exploits, but phishing is endlessly adaptable. The two options for mitigating risk, which are not mutually exclusive, are cultural change in the organization and a mandated standard of technical literacy for all employees and contractors with access to organizational resources.

Greg Kelley
Greg Kelley is CTO for Vestige, Ltd, a company that performs computer forensic services and data breach response for organizations.
The one mistake companies make that leads them to fall victim to phishing attacks is...
First, their employees are not cautious enough to question whether they should open an attachment or click on a link to a site without verifying that the attachment is legitimate and the website is valid. Employees likely have a false sense of security that their anti-virus would catch any attachment if it is bad. Employees also do not look to see where the URL they are about to click on will send them, and when they get to the site, they do not review the address for validity or if their browser is reporting a properly authenticated SSL certificate.
Second, the bad guys are getting good at social engineering. They are doing their research on companies, reading blogs, news articles and other information to determine who works at a company, what their email address is, what their position is and with whom they might be communicating. The result is a well-crafted spear-phishing email catered to the recipient.
These attacks cannot be prevented but they can be mitigated. Companies should train their employees in regard to email use and detecting phishing attacks. This training should be done at onboarding for new employees and everyone should get a periodic refresher course. Companies should also review what information of theirs they make public and carefully consider what information should be made public and what should not.

David Ting
David Ting is the CTO at Imprivata.
The one mistake companies make that leads them to fall victim to phishing attacks is...
Most organizations have reinforced their perimeter defenses, but attackers have turned to exploiting the inherent vulnerability of employees. Spear phishing attacks, for example, use cleverly disguised requests for login credentials (i.e., to install a security patch or upgrade their Microsoft Office software) to dupe unsuspecting employees into entering their usernames and passwords. Spear phishing and similar attacks hinge on users being responsible for discerning the difference between a legitimate screen and malware requesting login information. Even for well-informed users, this task is increasingly more difficult as attackers get more sophisticated. When employees are left with the responsibility of determining the legitimacy of a request, the results can be disastrous - it only takes one or two users to compromise the entire system.
To address this, organizations can leverage a multi-layered approach to security. Single sign-on (SSO) and strong authentication, for example, eliminate the need for employees to ever manually enter passwords to access systems, applications or information. If an organization has SSO and an employee is asked for credentials, there is a strong likelihood it is a phishing attack. What's more, these systems can be configured such that your employees would not even by able to manually enter passwords, even if they wanted to, because their password strings would be unknown to them.

Tom Clare
Tom Clare leads corporate and product marketing at Arctic Wolf and brings over 20 years of security marketing management to the team. Prior to joining Arctic Wolf, he led product marketing at Websense for their TRITON security solutions and Blue Coat for their Secure Web Gateways.
The one mistake companies make that leads them to fall victim to phishing attacks is...
People will open and click on email links, even more so when they are expecting an email for a delivery, an IT alert or a seasonal tax status notification. Phishing and spear phishing rank high in security analysis reports because the tactic works. The age old premise of a secure perimeter with preventive defenses has passed. A balance between preventative and detective defenses is required. Simply put, the preventative guards detect known bad and then the detectives need to find the unknown, such as hidden infections, open exploitable vulnerabilities, misconfigurations and security risks.
Start with the assumption that phishing email links will be clicked, providing cyber attackers the opportunity to move past your preventative defenses. The question is then - are you running continuous monitoring detective defenses? A solid baseline of monitoring will provide a normal range to then determine abnormal activity. Statistical and behavioral baselines are one form of machine analysis, plus pattern recognition, signatures and white listing. More advanced analysis uses data correlation models often provided within Security Information and Event Management (SIEM) solutions.
Detective defenses are also finding value in visualizations, providing the human eye the opportunity to pick out anomalies much faster than machine analysis. In narrow cases like fraud, machine analysis is effective, however for advanced persistent threats (APTs) often introduced through phishing emails, wider visibility and depth is required. Security analysts need the ability to search, pivot and trace with an analytical mindset.
Given people will click on phishing email links, you have to collect and look at the data to see infections and nefarious activity in your network. Ask yourself a simple question, what is the ratio of your preventative to detective defenses? This simple ratio is likely to answer the question about preventing and detecting phishing attacks.

Luke Zheng
Luke is the engineering lead at Stanza and a former engineer at Microsoft and Tesla. He's a graduate of Carnegie Mellon CS.
In my opinion, the one mistake companies make leading to phishing attacks is...
Mid to large companies often re-forward emails that are originally sent to one or two people. However, the recipients can be many, which increases the chances of multiple individuals clicking on a single email. Given the event of a phishing email, the chances of open rates/outbound clicks greatly increase in a model like such. A good way to prevent this scenario is to not only have phishing filters for any emails inbounding, but also prevent re-forwarding of emails to multiple people or distribution lists.
Smaller companies (startups) often have their founders as main points of contact via email. They also often use the same founder emails as logins for a wide range of websites. The chances of phishing increase with more inbound emails. Once a particular email gets sent using the identity of a founder, the legitimacy increases once forwarded to others in the company. This will result in more chances of outbound clicks even on a smaller group of individuals. A good way to prevent this is to not associate one email as the login for many websites, and not have founders be associated with such addresses.

Derek Dwilson
Derek Dwilson is a security expert and attorney. Derek has been passionate about technology and security his entire life. He has a law degree from the University of Texas and he has led the security, IT and legal ventures of Texzon Utilities. He currently consults with businesses on security solutions.
In order to prevent phishing attacks from succeeding, companies must remember...
Phishing is a problem on two fronts. First, a hacker may gain valuable access to a single account through a successful phishing attempt. Second, if an employee is using the same password for multiple company accounts, then the hacker has now gained access to a great deal of confidential company data.
On the first front, there are several warnings signs to look for. Often, Gmail will give you a warning near the subject line if the email sender looks phishy. A second line of defense is your browser. If you're visiting, for example, a fake PayPal site, then you may see a popup or icon indicating that something is suspicious. Employees should be trained to look for these warning signs. But they should also be trained to never give out sensitive information over the phone or by just clicking on a link in an email. Instead, if a credit card company calls, call them back using the number on the back of your credit card. If you get an email from PayPal, don't click on the link. Instead, go to PayPal directly.
On the second front, one can secure the company by using SSO tools such as LastPass and Yubikey. LastPass Enterprise allows employees to only have to worry about remembering one password, while creating a unique password for each log in. If you only use one password per account, then a hacker’s password bank will only be useful for that one hacked account. And because companies are often aware of break-ins and notify the public, LastPass can easily let you know which account passwords need to be changed.
But in addition to making sure each employee uses his or her LastPass password ONLY for LastPass, there is another layer of protection that you should set in place: YubiKey. YubiKey acts as a second factor in “two-factor authentication.” This ensures that no one can hack into your LastPass account. If all your passwords are created through LastPass and YubiKey adds a layer of protection to LastPass, then your accounts will be very difficult to break into.

Amit Ashbel
Amit Ashbel is a Product Marketing Manager at Checkmarx in Israel.
In my opinion, the one mistake companies make leading to phishing attacks is...
Phishing attacks are not what they used to be. Back in the old days, spammers and scammers used to send mass email campaigns leading people to a false web-site. The techniques have adapted since. Nowadays targeted attack tactics are more popular.
It works like this:
- Mark your goal - What do you want to gain? Money, Information, PII, CC numbers.
- Choose your target - Locate the correct VP, Director or C-Levels. Selecting your target depends on what you want to achieve.
- Perform a Background check - Plays golf, Married, 2 kids, Favorite car, anniversary coming up soon and liked Flower.com on FB.
- Launch your attack - Send a congratulation email from flowers.com including a link for a free anniversary gift.
The idea is to gain the victim's trust by using information they feel secure with. Take that and add a free gift with a malicious link and you have yourself a successful spear phishing attack. The link could download a piece of malware for financial or espionage purposes, or could trick the victim into giving out their CC number or other sensitive information.
Spear phishing attacks require more preparation however have a better success rate.
How to protect the organization:
- Employ clear guidelines - If you know the sender, be hesitant. If you don't know the sender, either check with your IT department or delete the email.
- Educate employees to use the web securely.
- Invest in security controls for cases where your employees make a mistake... they will.
- Analyze your internal development processes to make sure your internal applications are not easily exploitable whether containing employee data or financial statements.

Ashley Schwartau
Ashley Schwartau has been with the Security Awareness Company for over a decade, with experience in every part of the creative process, from conceptualizing and design to implementation and delivery. She works on every single client project that comes in the door, helping companies make awareness training effective, whether it’s short awareness videos and custom e-learning modules or a large global-scale awareness campaign. Her specialties include video editing, graphic design and creative problem solving. When she’s not making up new ways to present old ideas, she writes fiction, watches a lot of Netflix and walks her cats in the yard.
In my opinion, the most important step companies should take to protect against phishing attacks is...
EDUCATE your users.
Remind them about it on a regular basis. It's not a one-and-done situation. We all need reminders on a regular basis to drink our water, eat our vegetables, stand up when we've been sitting too long, to recycle… we also need reminders about changing our passwords and what to look for in phishing emails. Especially since phishing emails are getting more sophisticated.
TEST your users.
You can do this in a number of ways. Quizzes (after training), games, or periodic phishing campaigns against them. Companies like PhishMe and PhishLine offer these kinds of services that allow you to create phishing campaigns that tell you how many people clicked on the links so you can offer them more remediation and training.
Companies fall for phishing attacks due to not training their employees and assuming that people know more than they do. A lot of people leave their common sense at home or just have too much on their minds when working and click too fast. They see something and click instead of thinking hey that doesn't look quite right... People need to slow down and think before clicking, and companies need to educate their users about the risks of phishing emails. If the employees don't understand the risks associated with clicking on phishing links, why are they going to stop? If you educate them about the risks (to both the company and to the employee on a personal level), and teach them what to look for in phishing emails, then the number of clicks will go down.
Peter Moeller
Peter Moeller is the Director of Marketing for Scarinci Hollenbeck, LLC a 5 office, 55 business attorney law firm that has an extensive Cyber Security & Data Protection practice in NY/NJ/DC. He is the key driver of firm marketing initiatives including the implementation of a full scale web 2.0 lead generation platform. He leads a marketing team, vendors, and technology to drive business growth and increase brand awareness.
In my opinion, the one mistake companies make leading to phishing attacks is...
Phishing attacks are very sophisticated and tactful and come in many different forms of communication. Most phishing attacks will come in the form of an email, although they can also come by websites, physical mail or by phone calls. Companies tend to fall victim to attacks if they: 1. Do not educate their employees and 2. Don't have a system in place that can flag communication that might be malicious.
Preventing phishing attacks can be easy but it takes education and having plans in place to protect your company if something does slip up. First and foremost, it is vitally important to educate ALL of your staff on best internet/email practices. Educating your staff will allow them to question communications that don't seem right and will also allow them to follow best practices in order to investigate the communication they received. Have someone knowledgeable about phishing activities in place to help employees screen questionable communications. Make sure you teach all employees to never click on links, or open emails with specific file types, such as .exe files. Always open separate web tabs and research the email, sender, or links that are coming in. More often than not, you will receive immediate search results that flag the information as Spam and or being malicious. Educating your staff once is not enough. Constant reminders and updates should be conducted. When a phishing attempt is caught, share it with your staff, so they can familiarize themselves with how they look and feel. Having your staff on board and on the lookout for these type of scams will increase your chances at protecting your firm overall.

Nick Santora
Nick Santora is the chief executive officer at Curricula, a cybersecurity training and awareness company headquartered in Atlanta, GA. Prior to Curricula, Nick worked as a cybersecurity expert at the North American Electric Reliability Corporation (NERC), an agency that ensures the security and reliability of the bulk electric system in North America.
In my opinion, the one thing companies must do to stay protected against phishing attacks is...
Continuous cybersecurity training and awareness. We are reinforced on a daily basis to not talk to strangers, be careful with what we eat, save our money for retirement, say please and thank you, etc. How often are we reinforcing current cybersecurity threats and educating our staff on a routine basis? Until organizations take initiative to educate their people, we will continue to see alarmingly high engagement with phishing emails.
 Anne P. Mitchell
Anne P. Mitchell
Anne P. Mitchell is an Internet law and policy attorney, an Internet security expert, and heads the Institute for Social Internet Public Policy (ISIPP).
Here is something that is rarely talked about, and yet is a way that companies fall victim to phishing attacks on a regular basis...
Nearly every email program uses the 'from' section of an inbound email to display the contact's 'friendly name' (i.e., Anne Mitchell, rather than [email protected]) and photo. All it takes is the phisher spoofing a known email address, and the recipient automatically trusts it, never imagining it could be from anyone else, let alone a scammer. In fact, this is exactly how Medidata was phished out of more than $4 million. (We wrote this up here.) So, to prevent this sort of phishing or at least to not make it so easy for the scammers, we recommend that companies disable the display of friendly names and contact images in their email clients.
 Tom Kemp
Tom Kemp
Tom Kemp is the co-founder and CEO of Centrify, a leading provider of cloud-ready Zero Trust Privilege to secure modern enterprises.
I personally have seen an uptick in CEO fraud attempts, whereby crooks use social engineering and spear phishing to get executives to wire funds to crooks...
Going back to 2015 and continuing today, someone at Centrify receives an email from Tom Kemp, the CEO asking to help initiate a wire transfer on a monthly basis. That cadence has increased to a weekly or twice-weekly experience.
The scammers are also being more targeted now in terms of who they contact. Historically, they have done simple LinkedIn or Google searches and then gone after the HR manager, payroll clerk or finance director. But now, they know a bit more about our organization. This may have to do with recent breaches of B2B companies that aggregate a lot of information about employees at companies.
What to do?
- Educate employees on CEO fraud.
- Always pick up the phone and call to confirm an out-of-band request, even if you think the CEO may be mad.
- Implement multi-factor authentication on critical business applications.
A newer technology that anti-spam and email security vendors offer is the ability for security solutions to issue a warning when they see an impersonating email coming in.
For example, the email security system that Centrify uses internally produces the message, Warning: The Display Name used in this email matches an internal employee's name, in the subject line. It's very helpful to flag these types of email and I would highly recommend turning on this switch.
 Jacob Ackerman
Jacob Ackerman
Jacob Ackerman is the Chief Technology Officer at SkyLink Data Centers in Naples, Florida.
The biggest cybersecurity threat for businesses evolves from their people...
People are the biggest security risk. People are the target. I recommend that companies test their staff with fake phishing emails. Exercises like this will create a level of awareness and preparedness amongst the team.
People are the easiest way to gain access, especially given all the great technology tools like firewalls, etc. For example, something as simple as a sticky note posted on a computer monitor with a written down username and password reminder might be all a hacker needs to penetrate your network. A hacker could subtly angle their camera phone to grab a pic of it in the middle of a casual conversation with the associate at their desk.
Your IT people can't protect you from maintenance uniforms! If you have third party office cleaning, air conditioning, and other vendors walking through the office (especially after hours), any password information left available on desks is a risk.
Stop your staff from writing down passwords and storing in a drawer or under their keyboard. Also, business owners or technology leaders that are in a first floor building should regularly walk around the perimeter outdoors and inspect what can be seen through windows. You may be surprised what kinds of information staff have visible at their work space.
Business owners shouldn't only be concerned about security threats from fancy computer scripts, phishing emails, ransomware, malware, etc. but the lack of password policy inspection and enforcement happening right in front of them daily. These are all low cost prevention tactics that have high impact on protecting a business.
 Aidan Simister
Aidan Simister
Having worked in the IT industry for a little over 22 years in various capacities, Aidan is a veteran in the field. Specifically, Aidan knows how to build global teams for security and compliance vendors, often from a standing start. After joining Lepide in 2015, Aidan has helped contribute to the accelerated growth in the US and European markets.
Lack of employee education is the main reason that employees click on phishing links...
Phishing emails are becoming more and more complex and targeted. With the mass of data beaches that have happened within the past year, cyber criminals are able to tailor an attack to that individual.
The first place to start is to train all employees, managers, and third parties to spot phishing emails, and make sure they are fully aware of their security responsibilities. If your employees know how to spot a potential phishing attack, they will be far less likely to fall for it. One of the best ways to ensure that your staff are vigilant in spotting potential phishing emails is to carry out a simulation. Send out an illegitimate email to all staff members asking them to click on a link, and then monitor who and how many people go through with it.
Whenever possible, use multi-factor authentication, which can prevent the attacker gaining access to your system even if they manage to gain access to a user's login credentials. Grant employees with the least privileges necessary for them to do their job. This will at least minimize the attack surface, should the attacker manage to obtain an employee's login credentials. F or example, if one of your junior employees falls victim to a phishing attack, the impact will be fairly minimal as their access levels should be limited. If, however, a senior administrator falls victim to the same attack, the malware could leverage domain account privileges to affect servers, endpoints, and sensitive data from across the entire network.
 Mike Baker
Mike Baker
Mike Baker is Founder and Managing Partner at Mosaic451, a managed cyber security service provider (MSSP) with expertise in building, operating, and defending some of the most highly-secure networks in North America. Baker has decades of security monitoring and operations experience within the US government, utilities, and critical infrastructure.
Phishers often perform research before launching their attack...
Hackers examine the target company’s website and social media networks and learn about the company’s employees, their positions and responsibilities within the company, even their personal interests and hobbies – anything that they could use to make the phishing email look more genuine.
Phishing has become a great sport for cyber criminals because they offer a simple but highly effective cyber attack vector that takes advantage of the most vulnerable of prey – humans! One of the human vulnerabilities phishers exploit is employee desire to please bosses or authority figures. Employees should be encouraged to ask questions about any requests that seem “off,” even if the request appears to have come from a top executive.
Because phishers scour company websites and social media networks for personal information on executives and employees – and information about the company’s activities, such as new clients and new markets – businesses (or anyone) should be cautious about what they post publicly on the web. Likewise, organizations should educate their employees on the dangers of posting too much information on their personal sites. A hacker looking to launch a phishing attack may examine employees’ personal social media feeds as well.
What steps could organizations take to protect themselves from phishing scams?
Organizations cannot depend on email spam filters to prevent phishing. While spam filters intercept most regular phishing emails, imposter emails often bypass them because only a few emails are sent at a time, and they do not contain wording that spam filters pick up on (like “porn”). Hackers take time to make them look like legitimate business correspondence.
Know the telltale signs of phishing emails. Although phishers go to great lengths to make their emails look legitimate, many attacks originate overseas, with the emails composed by hackers who are not fluent in English. As a result, the email may use British spelling, contain punctuation, spelling, or grammar errors, or be worded oddly. The salutation or the closing may also be off. Also carefully examine reply-to addresses and look out for spoofed domains that are only slightly different from the company’s actual domain.
Establish protocols for wire transfers, payments, and the release of sensitive information. Implement a payment system that requires a purchase order that is approved by both a manager and a finance officer; a multi-person approval process for transactions exceeding a certain dollar amount; and phone verification of all fund transfer requests and any changes to vendor payment information. Likewise, the release of employee W-2 data and other sensitive information should be subject to the approval of multiple parties and a verification process that ensures the party requesting it has the legal right and a legitimate reason to access it. Further, company policy should prohibit highly sensitive information – whether bank account numbers or employee Social Security Numbers – from being transmitted via email.
Conduct regular penetration testing. Organizations should have their internal security staff – or enlist the services of a managed security services provider (MSSP) – conduct regular penetration tests aimed specifically at social engineering techniques such as phishing. These tests involve “good guys” sending “phishing” emails to employees and executives to see if they click on them or report them. The results can be used for employee education and, if necessary, for restricting the system access of certain users.
Encourage healthy skepticism. Establishing strict and specific authentication protocols helps with this; if employees know what the company’s protocol is, they are better able to recognize requests that do not appear to follow it. But, that will never work 100%, so organizations need endpoint protection in concert with content monitoring/filtering.
 Jackie Rednour Bruckman
Jackie Rednour Bruckman
Jackie Rednour Bruckman is the Chief Marketing Officer for MyWorkDrive.
Companies and organizations easily fall victim to phishing attacks often during...
Rushed times of checking company email on their phones and devices and not properly vetting an email with a directive to click a link. Before they know it, they have unknowingly reset a password or given some information that allows a bad actor to penetrate and compromise their company network. This scenario made headlines during the Presidential campaign of 2016 when Clinton Campaign Manager, John Podesta got a phishing email looking like a Gmail request to change his password for security reasons. In minutes, thousands of emails were in the hands of hackers.
This scenario could have been avoided by a simple password security protocol aggressively messaged and adhered to by staff. In particular, any request for password updates, security email links, etc. should be forwarded on to IT and Security staffers for vetting, and the user then deletes the email out of the inbox entirely.
Better yet – a solution would involve not using any public cloud platform at all for high risk emails, high profile accounts, and high level secure communications. Using an Exchange server set up behind firewalls would have helped during this scenario. A strict computer usage policy must be created, messaged, and adhered to for any organization large or small in this digital age. This includes some simple rules like no clicking on links or attachments from anyone not known and unfamiliar.
Aggressive malware protection must be on the networks and kept current and working as well. Data leak and data loss prevention must be part of any enterprise structure and strict protocol must be followed for any remote logins and remote desktop situations as mobile device management becomes part of enterprise network security.
 Idan Udi Edry
Idan Udi Edry
Idan Udi Edry is the CEO of Trustifi, a software-as-a-service company offering a patented postmarked email system that encrypts and tracks emails. Before his work with email encryption, Idan served as an Israeli Air Force officer for more than eight years, reaching the rank of captain and leading hundreds of professionally trained military personnel in building and operating advanced information systems. A trusted authority in information technology and data security, Idan has 13 formal certifications from the most renowned IT and telecommunications organizations.
Cybercriminals are getting smarter with their attacks, and with a major increase in email breaches and data compromises this year...
There are more security measures to make sure are always implemented. Year after year the number of cyber scams increase due to malware and spear-phishing campaigns. To prevent this type of attack from compromising your information, it is EXTREMELY important to pay attention to where emails are coming from. Many cyber scammers spoof large company mass emails with similar subject lines or body content hoping you won't notice. Always look at the email address; this will let you know immediately if the email is coming from a reliable source or not. If you aren't sure, don't negligently download or click on malicious files in an email resulting in ransomware or other malware being downloaded onto the computer.
People are often unaware of another phishing method cyber attackers implement to access your information, and that is through Wi-Phishing. Hackers often use Wi-Phishing to try to trick you into logging on the wrong network to get ahold of your information. Always ensure your network is private with servers protected by firewalls and anti-virus/malware software. When using public Wi-Fi, always check that you pick the most legitimate network. It's also best to pick a secure network hotspot that requires some sort of password to allow usage access. Most laptops and cellular devices have their own hotspot abilities. If you ever are questioning your safety you can try this option. It won't be very fast, but it will be more secure.
 Chris Gonzales
Chris Gonzales
Chris Gonzales is one of the premier network strategists in the Southeast United States with numerous certifications and decades of consulting with highly regulated industries including banking, healthcare, and manufacturing. He joined My IT in 2012 as the company's operations manager and rose through the ranks to Chief Technology Officer and, now, Chief Operating Officer. In 2016, Chris was named one of New Orleans CityBusiness' Ones to Watch in Technology.
Companies, large and small, fall victim for phishing attacks because they rely on one or two mechanisms, such as a firewall and spam filter, and think that they are bulletproof...
No layer of cybersecurity is immune to penetration, especially with zero-day attacks (first time a virus is seen). We layer multiple layers of security including firewalls, email and web filtering, security-operations-center, threat sweeping, and user training.
User training has been one of the most effective ways to eliminate threats because attacks can slip by hardware and software. Many phishing attacks contain no links or attachments, so they do not raise any flags with spam filters and other protection methods.
Additionally, phishing attacks work because companies have poor approval processes in place. Accounting should never send money anywhere and HR shouldn't send confidential data per an email request from the CEO or CFO without verifying by another means such as a text, phone call, or just walking down the hall and talking to the person.
 Michael Brengs
Michael Brengs
Michael Brengs is a recognized identity management expert and industry speaker who has been deploying identity management solutions for 20+ years and is currently a Managing Partner with Optimal IdM. Mr. Brengs attended the University of South Florida where he earned a degree in Management Information Systems and is a Microsoft Certified Professional.
First, phishing emails are crafted to look legitimate, such as saying Bank of America Customer Service for the display name of the from in the email...
But if you look at the detail of what the real email account is, it may be something entirely different. Some common red flags to identify a phishing e-mail:
- Be sure to look at any hyperlinks by hovering over them before you click. The text of the hyperlink might look legit but the actual redirect URL could be something bogus.
- Look for misspellings or poor grammar. Many scammers are not native English speakers and make grammatical mistakes.
- Never give up any personal information from an unsolicited email. If your gut says this is fishy, it probably is phishy.
- Do NOT click on any attachments from unknown sources. If this is your corporate email, notify your IT staff.
If you receive a phishing e-mail, delete it, do not click on any hyperlinks. Do not respond to the email. Empty your trash folder. Alert your corporate IT department that you were being phished. If you fall for a phishing scam, reset the password for that site you thought you were logging into. Do NOT use a password similar to another site's password. Monitor that account closely for at least 90 days on a daily basis. If it was banking or another sensitive nature, contact their IT department and let them know the situation.
 Marc Enzor
Marc Enzor
Marc Enzor is the President of Geeks 2 You, an IT consulting Firm. Marc has spent the last 22+ years working on cybersecurity for small to medium size businesses.
Phishing attacks have become a daily threat for every organization, and they aren't slowing down anytime soon...
The problem is, they work exceptionally well. Attackers have even started Spear Phishing attacks; these are attacks that are highly targeted. I've seen fake emails looking like they came from the CEO of an organization sent directly to Accounts Payable departments, asking for wire transfers to random bank accounts, telling them to only let me know when it is completed and that they are under a deadline. When the CEO demands you do something, you are used to doing it immediately and not questioning. So how do we solve these serious threats?
The primary answer is that IT departments need to simulate attacks and train the victims. There is a plethora of phishing testing services that will allow IT/Cybersecurity teams to craft fake phishing attacks and send it out to all the employees of the organization. It'll then report on who fell for the attack and clicked the link or provided their password. IT can then subject those victims to special training so they know what to look for, and how to avoid being a victim in the future. This is the only comprehensive solution that can be proven to work.
Other efforts can and should be made to upgrade email firewalls and add in specialty filtering for common phishing attacks. When it comes to specialized spear phishing emails, they will always be difficult to stop. The more research the attacker puts in, the more likely their attack is to succeed. The attackers are quickly learning this, and will only become better at evading spam/phishing filters, and reaching their targets. Other efforts should be made to train staff to always double- or triple- verify all bank transfers. Lastly, email accounts should have mandatory password expirations set to 90 days, so employees are forced to change their passwords often. This will automatically patch up any passwords that may have been taken during a phishing attack, and will eventually block out attackers.
 Aaron Birnbaum
Aaron Birnbaum
Aaron S. Birnbaum is the Chief Security Officer at Seron Security. Mr. Birnbaum has nearly 30 years of consumer and business sales, partnership, and marketing experience. He has worked with companies of all sizes – from Fortune 500 to startups and has extensive experience with a number of different industries. Mr. Birnbaum has the unique ability to initiate ‘win-win’ discussions, explain clearly and concisely how technology works in a granular ‘easy to understand’ level, and to work successfully with many diverse types of people. As Founder and Principal of CITM, Mr. Birnbaum helped a variety of small to midsize companies by developing business plans, marketing strategies, sales programs, and recommending new technologies. He has worked across a broad spectrum of industries and has personal relationships with many Fortune 500 companies including AOL/Time Warner, Amtrak, MCI/WorldCom/Verizon, Burger King, Citicorp, Coors Brewing Company, Hill & Knowlton, P&G, Coca-Cola, Bank of America, Weiden+Kennedy, Puma, and Nike.
There are several different reasons that businesses become victims of phishing attacks...
Three of the most popular being: inadequate security training, a lack of security policies, and a lack of proper social media usage. By providing regular security awareness training to employees, a business can drastically reduce their risk and exposure to these attacks.
Phishing is a method of gaining access to a network, a person or a company's private information with the implied intent to do harm. There is 'spear phishing' - targeting a specific individual, usually after gathering data on social media websites, 'clone phishing' – where a user is fooled by a legitimate-looking email that contains an attachment or bad link, 'CEO fraud' or 'whaling' – where the target is a senior person in the company and requests an employee provide verbal or in writing private confidential information, or is persuaded to send money or information to an impersonator or an external source. General phishing is an attack where a user is directed to download an attachment or visit a copy of a reputable site but that is hosted on a different domain. There are also techniques called 'vishing' and 'smishing' that utilize the same techniques on voicemail and SMS or text messaging.
The most popular goal of this can be achieved by persuading a user to download malicious software (malware) compromising the network the user is operating on. This can be done by disguising an email attachment with a common name (e.g. 'spreadsheet.xlw', or 'file.pdf'), or by directing a user to click a link to visit what they think is a safe site. A common example would be a notice from your bank that your account has been compromised and you need to click a link to reset your password. When you click the link in the email, you are directed to a website that looks very much like the real site, but is hosted at a different location. An example of this might be a request to update your password at 1inkedIn.com or Linked1n.com instead of the real website LinkedIn.com. Users that aren't paying close attention can easily fall victim to these tricks.
The best way to combat these threats is to educate the users that are targeted. Security awareness training programs can help teach users good habits, and should be followed up with sending fake emails to test the users. Users that fail should be retrained, disciplined or potentially terminated. Other methods include: Never click on a link in an email, open the browser and type the URL in manually. If you get a request from someone that seems 'strange' pick up the phone and verify the request. Have a security policy for employees with specific examples of how to deal with possible situations. Look for typos, poor grammar, misspellings or bad links to images in emails and websites.
Frequently Asked Questions
Why are phishing attacks so successful?
While some phishing attacks rely on dumb luck – simply sending hundreds of messages in hopes someone clicks a link or opens an attachment, other attacks can be increasingly refined to target a user; often referred to as spear phishing. When a phishing email is convincing and impersonates a known person or brand close to a user and that person is either multi-tasking or not paying attention, it can result in the perfect opportunity for a phisher.
In some ways, solving phishing attacks should be viewed through the lens of human behavior: It's human instinct to want to click through links. As the New York Crime Commission found in a study, “cognitive biases and heuristics can make users more vulnerable to phishing attacks.”
What are some common mistakes companies make that leave them susceptible to phishing attacks?
Organizations that fail to educate employees on the dangers of blindly clicking links and opening attachments from unknown senders are inviting risk to their organization. Some of the best security awareness programs should evolve to show the changing tactics of phishers, tips and tricks used to obscure URLs, and how to recognize a malicious link.
What are some defensive measures companies can implement to prevent phishing attacks?
- No matter how many solutions you use - firewalls, spam filters, etc. - there is no silver bullet when it comes to preventing phishing attacks. Consider taking a layered approach that incorporates training, e-mail security and anti-phishing solutions, and controls that can help security teams learn more about phishing attacks and prevent them from using similar vectors in the future.
- Consider having a strategy in place that mirrors the United Kingdom's National Cyber Security Centre's Four Layers of Mitigation:
- Layer 1: Make it difficult for attackers to reach your users
- Layer 2: Help users identify and report suspected phishing emails
- Layer 3: Protect your organization from the effects of undetected phishing emails
- Layer 4: Respond quickly to incidents
- Deploy a security awareness training program where you can conduct training sessions with employees to further educate them on phishing techniques and tell-tale phishing indicators. Test employees but don’t punish them when they fail; communicate best practices and educate.
- Use two-factor authentication, especially to safeguard accounts in which a user's credentials have been compromised
- When it comes to mitigating CEO fraud or whaling attacks, take the time to verify out-of-band requests for information or access.
Take Your Next Step
Towards Preventing Phishing Attacks
|
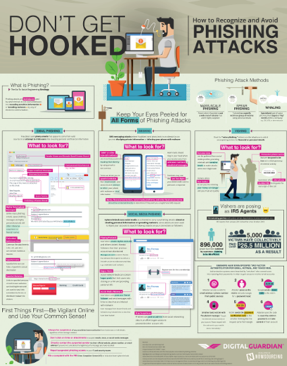
Promote phishing awareness at your organization with this free infographic poster. DOWNLOAD POSTER |
Develop an effective security awareness program in 5 steps, from Fortra's Terranova Security. GET THE GUIDE
|
Recommended Resources

All the essential information you need about DLP in one eBook.

Expert views on the challenges of today & tomorrow.

The details on our platform architecture, how it works, and your deployment options.